How IT Leaders Build Infrastructure Secure Communication Systems for Enterprises
How IT leaders can eliminate fragmented communication, migrate away from legacy systems, and build scalable, secure infrastructure for hybrid work without disrupting the business in the process.
Why Enterprise Communication Security Breaks Down at Scale
Most enterprise communication failures don't start with a breach. They start with a spreadsheet listing 14 different tools that no one agreed to buy.
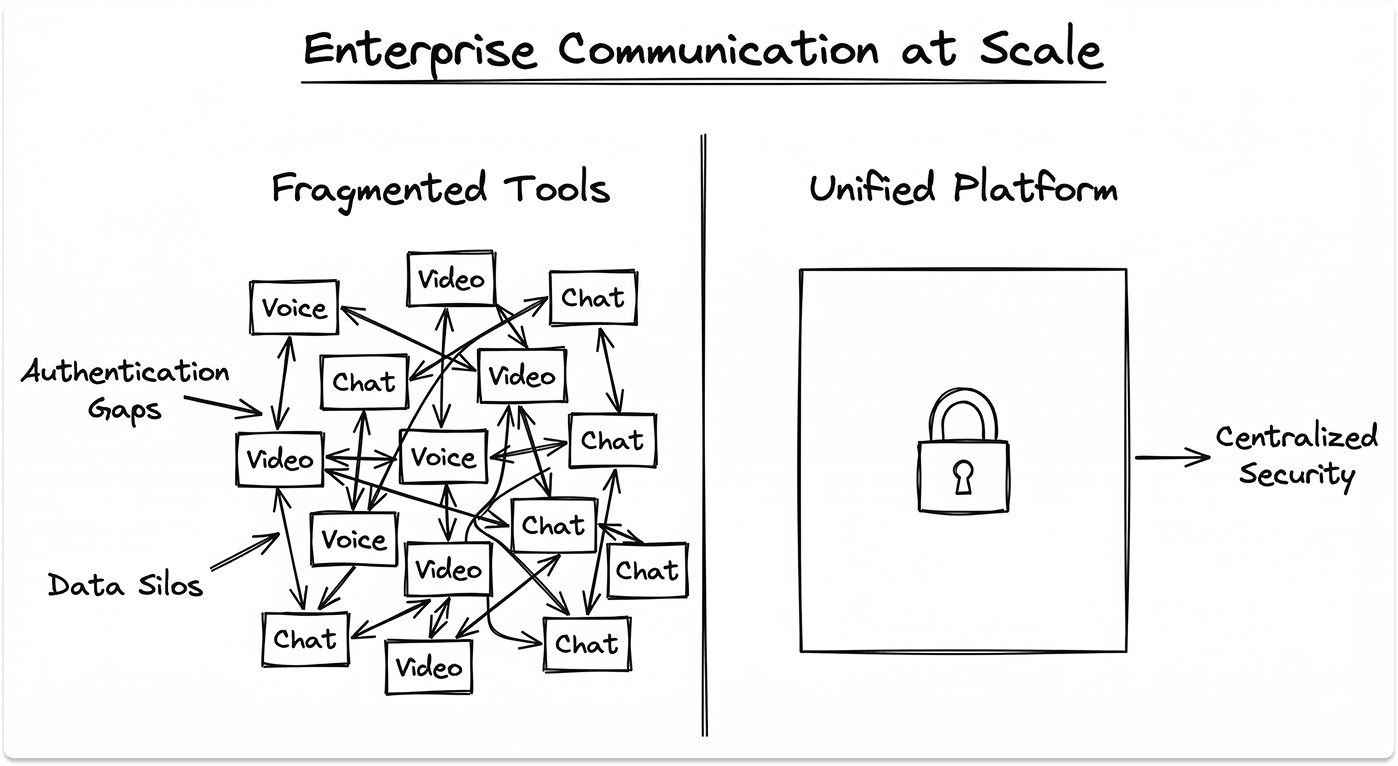
Voice calls on one platform. Video on another. Messaging scattered across three apps. File sharing on a fourth. Each one was deployed to solve a specific problem, and each one introduced a new surface for attackers to exploit, a new vendor to manage, and a new place for critical information to get lost.
According to an analysis of workplace communication data, 73% of workers now report an increased variety of communication channels, and 54% struggle to manage the volume that comes with it. That's not a productivity problem. For IT leaders, it's an infrastructure problem.
Every additional communication endpoint is an authentication gap. Every unsanctioned app is a data residency question. Every siloed tool is another integration your team has to maintain, monitor, and patch. And when something breaks, it's your team fielding the tickets.
Scale compounds this. A 50-person company with fragmented tools is an inconvenience. A 5,000-person organization with the same fragmentation is a security incident waiting for a date.
The Real Cost of Fragmented Communication Tools
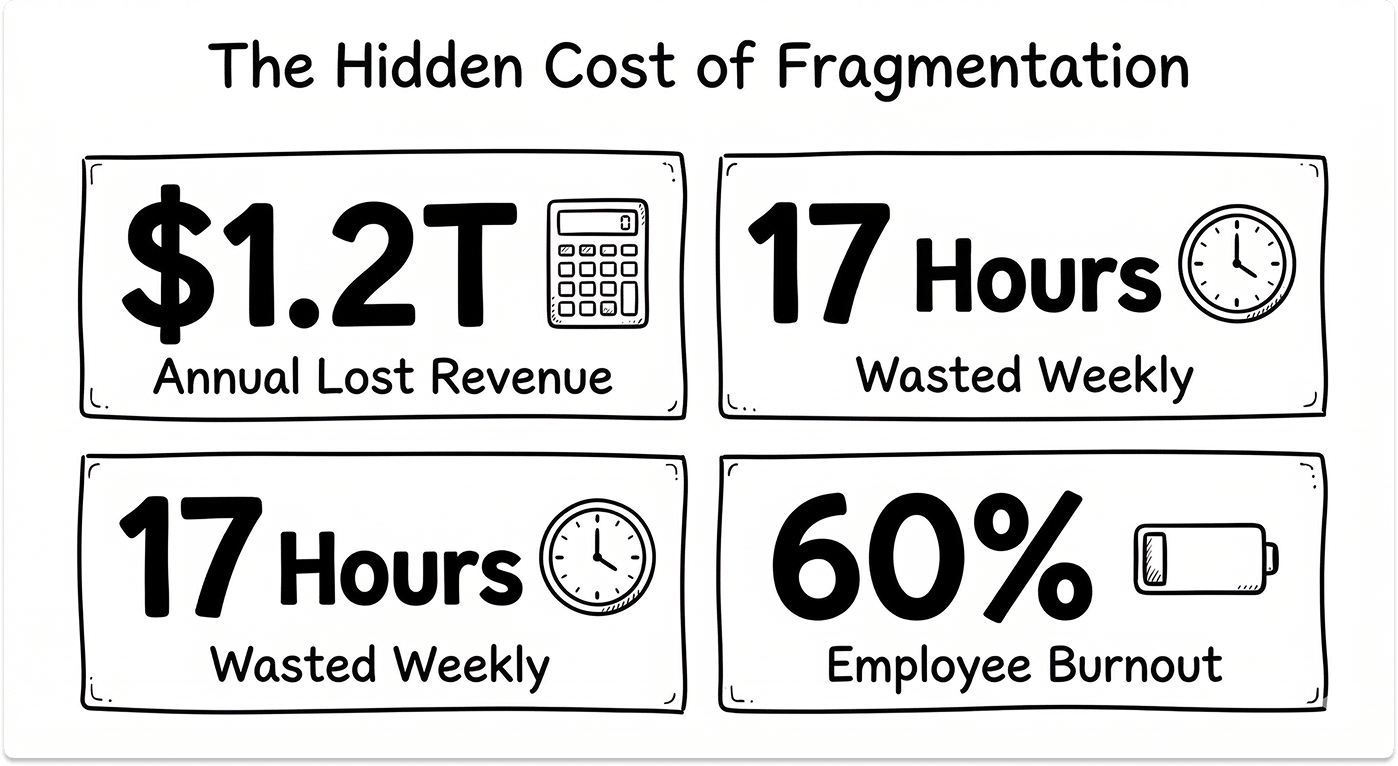
The financial case for fixing this is straightforward. The annual cost of poor communication for US businesses is at $1.2 trillion. One in five business leaders has lost a deal or a client directly because of communication failure. Knowledge workers spend an average of 17 hours per week resolving ambiguous messages alone.
For IT teams specifically, tool fragmentation drives a disproportionate share of the support burden. More tools means more provisioning, more user training, more integrations to maintain, and more security policies to enforce across a wider surface. Your team doesn't just inherit the communication problem. They own it.
The hidden cost that rarely shows up in a business case: burnout. The same data shows 60% of employees report burnout specifically from digital communication overload. When your infrastructure is fragmented, your people bear the friction of bridging the gaps manually. That cost lands on performance reviews, retention figures, and eventually your ability to recruit.
Fragmented communication also creates a ceiling on AI initiatives. When organizational data lives across disconnected systems with no unified layer, you can't feed it into AI pipelines reliably. IT leaders trying to extract real AI value from their infrastructure consistently identify data fragmentation as the first bottleneck they have to solve before any AI initiative can move forward.
When Legacy Infrastructure Becomes the Bottleneck
The on-premises PBX is the most visible version of this problem, but it's rarely the only one. Legacy email servers, outdated call routing systems, on-site hardware for video conferencing: these systems were engineered for a world where everyone sat in the same building, on the same network, behind the same firewall.
They are expensive to maintain, brittle under load, and nearly impossible to extend into modern hybrid work environments without layers of workarounds that create their own vulnerabilities. Every patch tightens the knot rather than loosening it.
The reason most organizations keep these systems running long past their operational life isn't technical. It's political. Fear of migration downtime. Uncertainty about ROI. Ownership disputes between IT and finance. The result is technical debt that compounds quietly until it becomes a crisis: a system that can't scale to a new office, can't support a remote workforce, can't integrate with the cloud tools the business has already adopted.
PBX migration is a decision that gets deferred until it becomes urgent, and urgency is the worst time to make infrastructure decisions. The organizations that handle this well treat it as a planned transition, not a forced one. Switching infrastructure providers without losing control of operations is achievable, but only when the transition is designed before the pressure hits.
How Hybrid Work Exposed the Gaps in Enterprise Communication Infrastructure
Remote and hybrid work didn't create the problem. It made the existing one impossible to ignore.
When teams relied on physical presence, fragmented tools were a nuisance. You could walk to someone's desk. You could catch a colleague in the corridor. Informal communication filled the gaps that digital tools left open. The infrastructure was held together by proximity.
Remove that proximity and the cracks become canyons. Teams that depend entirely on digital tools for every interaction find that when those tools don't work together, collaboration doesn't just slow down. It stops.
62% of workers now interact across different time zones. Hybrid teams working across locations have zero tolerance for dropped calls, missed messages, or tools that require workarounds to connect with colleagues on different systems. The communication infrastructure either works seamlessly, or it becomes a liability.
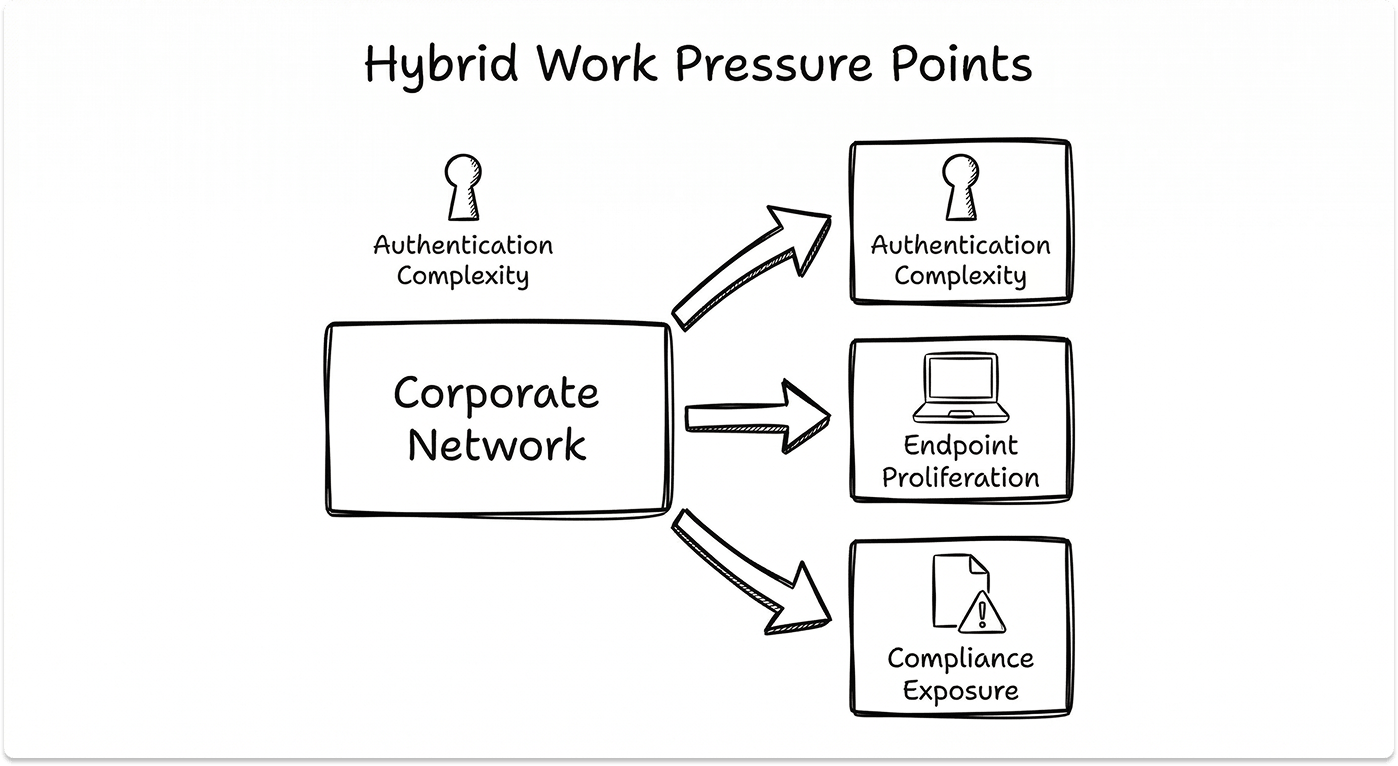
The hybrid work shift created three specific pressure points for IT:
- Authentication complexity: Users connecting from personal devices, home networks, and public Wi-Fi multiplied the number of contexts IT has to secure. A communication platform that works cleanly inside the corporate network may behave unpredictably outside it.
- Endpoint proliferation: Laptops, mobile phones, tablets, home office hardware. Every device is a potential entry point. Secure enterprise communication systems have to work across all of them without requiring the user to manage the security themselves.
- Compliance exposure: In regulated industries, fragmented communication creates a direct compliance problem. When sensitive conversations happen in consumer messaging apps because the corporate tool doesn't work well enough, the organization has no audit trail, no data governance, and no control.
Why Secure Communication Systems Have Become Non-Negotiable
Security in enterprise communications used to mean "don't use consumer apps." That bar is now the floor, not the ceiling.
IBM's 2024 Cost of a Data Breach Report put the average cost of a data breach at $4.88 million. Communication platforms are increasingly the attack surface. Phishing via collaboration tools, toll fraud on VoIP systems, call interception, and denial-of-service attacks on communication infrastructure are not edge cases. They are documented, recurring attack vectors.
The regulatory layer adds further complexity. HIPAA requires that patient communications meet specific encryption and auditability standards. GDPR mandates data residency and access controls that many off-the-shelf tools don't support by default. What enterprise buyers are actually asking about data protection goes well beyond basic encryption, covering audit logging, breach disclosure timelines, and AI data governance. Industry-specific frameworks pile on requirements that a single unsecured communication endpoint can violate.
The organizations that treat communication security as a baseline, not an upgrade, are the ones that avoid the audit findings, the breach notifications, and the remediation costs that follow.
What Scalable Communication Infrastructure Actually Looks Like
"Scalable" is one of the most overused words in vendor marketing. In practice, it means something specific: the ability to add users, locations, channels, and capabilities without architectural rework, without migration downtime, and without introducing new security gaps in the process.
A communication system that requires a full rip-and-replace every time the business acquires a company, opens a new office, or moves 500 people to remote work is not scalable, regardless of what the vendor brochure says.
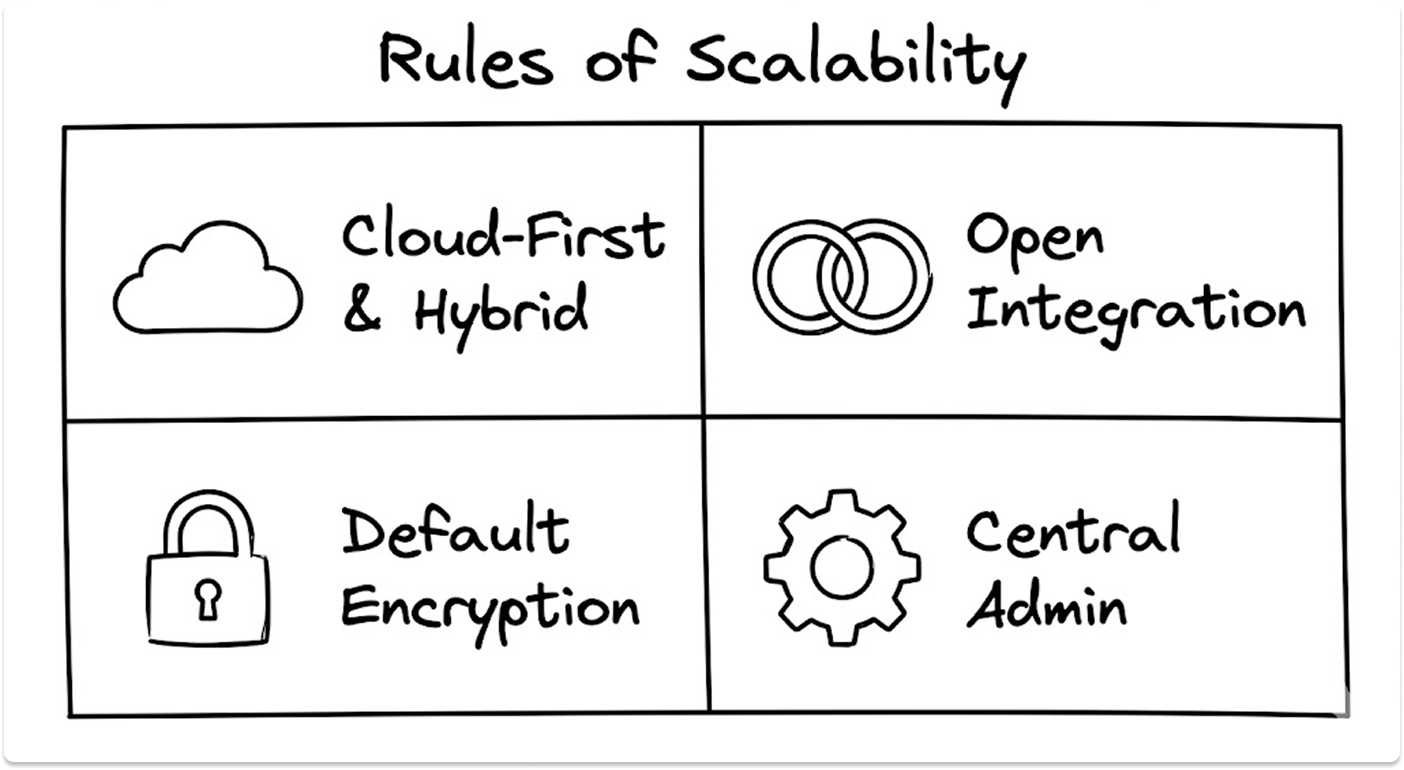
Genuinely scalable communication infrastructure has four characteristics:
1. Cloud-first architecture with hybrid support
Cloud-native platforms provision new users and locations in hours, not weeks. They separate the communication layer from the physical infrastructure, which means a new office doesn't require new hardware before people can start working. But scalability also requires hybrid support: the ability to integrate with existing on-premises systems during migration phases, so the business doesn't face a binary choice between old and new.
2. Open integration standards
The communication platform isn't the only system in the organization. It needs to connect with CRM, ITSM, HR, and security tools without custom development work. Platforms built on open APIs and standard protocols, SIP for voice and REST APIs for integrations, are far easier to extend than proprietary closed systems.
3. End-to-end encryption as a default, not an option
Encryption that's off by default and requires user action to enable is encryption that won't be enabled. Secure enterprise communication systems enforce encryption at rest and in transit as a baseline, across all channels: voice, video, messaging, and file transfer.
4. Centralized administration and visibility
A communication platform that IT can't fully observe is a platform IT can't fully secure. Centralized dashboards for user provisioning, policy enforcement, call quality monitoring, and security logging are what separate a communication tool from a communication system.
The Criteria IT Leaders Should Use to Evaluate Any Solution
Before any vendor enters a conversation, the evaluation framework should already exist. Here is the minimum bar:
- Uptime SLA: What is the guaranteed availability? Is there a compensation clause? What does the vendor's historical uptime actually look like, not just what's in the contract? A strong SLA management framework defines how you measure, monitor, and enforce these commitments independently, not just take the vendor's word for it.
- Encryption standards: Is end-to-end encryption enforced by default? What protocols are used? Has the platform been independently audited?
- Compliance coverage: Does the platform support HIPAA, GDPR, or industry-specific requirements out of the box, or do they require add-ons and custom configuration?
- Migration support: Can the vendor support a phased transition from legacy PBX, or does the migration require a hard cutover? What is the rollback plan?
- Operational management: Who is responsible for ongoing upgrades, moves, adds, and changes? Is that included or billed separately?
These aren't negotiating points. They are baseline qualifications. The 10 questions every IT leader should ask before choosing a vendor go deeper on how to stress-test vendor answers before any contract gets signed.
Any vendor that can't give direct, documented answers to these five questions is not ready for an enterprise environment.
What a Capable Enterprise Communication Partner Looks Like in Practice
For many IT teams, the honest constraint isn't knowledge. It's bandwidth. Designing, implementing, and managing a scalable, secure communication infrastructure is a full-time operational commitment. Teams already carrying the weight of existing infrastructure, security monitoring, and strategic projects rarely have the capacity to treat a communications overhaul as another internal workstream.
This is where a specialized implementation partner changes the equation. Not to replace IT judgment, but to execute against it.
The distinction matters: a capable partner brings implementation depth, not direction. IT defines the requirements, the security posture, the compliance constraints, and the integration architecture. The partner handles the build, the migration, and the ongoing operational load. Understanding how managed IT service providers operate, what they cover, and how to hold them accountable is worth knowing before that conversation starts.
Spadafy is one example of a vendor that fits this profile. They deliver a unified communications and collaboration platform built for organizations that expect to grow and can't afford operational disruption in the process.
Their capability set maps directly to the evaluation criteria above:
- VoIP Implementation: Spadafy handles both greenfield (new deployments) and brownfield (existing infrastructure) VoIP projects. Their involvement starts at architecture and design, not just installation, which means the foundation is built correctly before a single handset is provisioned.
- Meetings and Collaboration: Purpose-built for hybrid and remote workforces. The platform is assessed and configured to specific organizational requirements, not deployed off a standard template.
- Call Center Solutions: Platforms for both internal operations and external customer engagement, with a focus on security, high availability, and the scalability to grow with demand rather than requiring replacement when demand increases.
- Cloud Telephony: Migration from on-premises PBX to cloud-based telephony with enterprise-grade reliability. Reduces maintenance overhead and eliminates the upgrade cycles that consume IT time on legacy systems.
- Systems and Operations Management: Ongoing management for both cloud and on-premises environments. Upgrades, troubleshooting, moves, adds, and changes are handled operationally, meaning your internal team stays focused on strategic work rather than routine maintenance.
What Spadafy gets right is continuity. They don't deploy and walk away. The operational management piece is what allows organizations to treat communication infrastructure as a managed service rather than a recurring internal project. For IT leaders managing lean teams against a wide surface, that matters.
Building a Secure, Scalable Communication Infrastructure: The Path Forward
The organizations that get this right aren't doing anything exotic. They're making deliberate architectural decisions early, before scale or a security incident forces their hand.
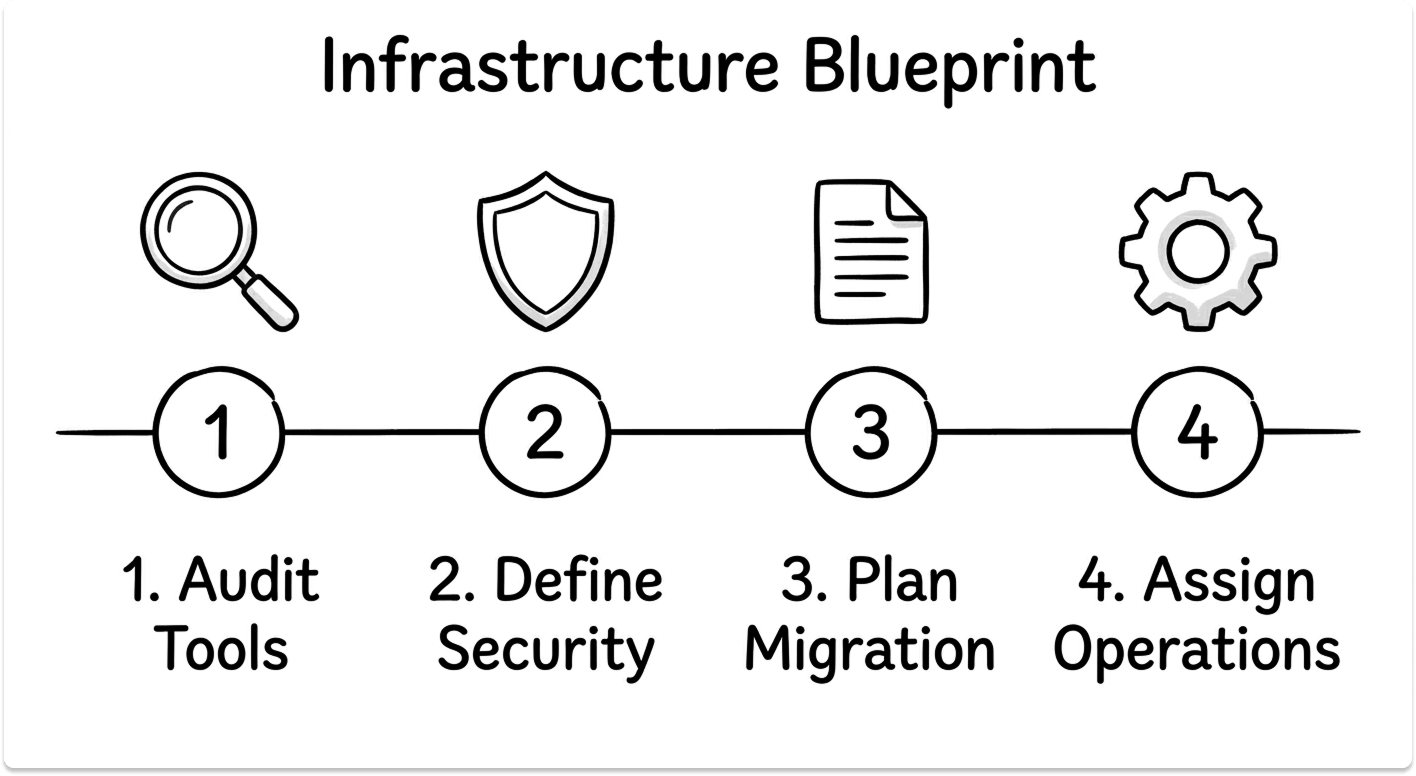
The path looks like this:
Audit before you build. Catalog every communication tool currently in use, sanctioned and unsanctioned. Understand what data flows through each one, what security controls exist, and what compliance obligations apply. Most organizations discover three to four tools being used at significant scale that IT didn't formally approve. That's your baseline.
Define the security posture first. Before evaluating any platform, establish what "secure" means for your organization specifically. Encryption standards, authentication requirements, data residency constraints, audit logging requirements, compliance obligations. Platforms are evaluated against those requirements, not the other way around.
Plan the migration, don't react to it. PBX migration and tool consolidation are disruptive when they happen under pressure. Organizations that plan a phased transition, keeping legacy systems operational during migration, running parallel environments where necessary, training users before cutover, absorb the disruption at a manageable pace. Those that wait for a system failure to force the issue absorb it all at once.
Treat operational management as a design decision. Who is responsible for ongoing maintenance, upgrades, and security monitoring of the communication infrastructure? If that question doesn't have a clear answer before the platform is deployed, the answer defaults to "whoever is available," which is how strategic teams become reactive ones.
Communication infrastructure that is secure, scalable, and operationally sound doesn't happen by default. It is designed that way, deliberately, before the business grows into it. The cost of getting it right upfront is a fraction of the cost of remediating it under pressure.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What are the main security risks in enterprise communication systems?
The primary attack vectors are phishing through collaboration platforms, toll fraud on VoIP infrastructure, call interception, misconfigured integrations, and unauthorized use of consumer messaging apps that bypass corporate security controls. IBM's 2024 Cost of a Data Breach Report identifies misconfigured integrations as one of the leading causes of communication platform breaches.
How do you evaluate whether an enterprise communication platform is truly scalable?
Focus on four things: cloud-native architecture with on-premises hybrid support, open integration standards (SIP, REST APIs), default end-to-end encryption across all channels, and centralized administration. Any platform that requires significant architectural rework to add users, locations, or capabilities is not genuinely scalable.
What does PBX to cloud telephony migration involve for enterprise IT teams?
A structured migration involves an audit of existing call routing, voicemail, and integration dependencies; a phased cutover plan that keeps legacy systems operational during transition; user training before cutover; and a rollback plan for the first 30 to 60 days. Organizations that treat it as a phased project absorb disruption incrementally. Those that do a hard cutover absorb it all at once.
Why is fragmented communication a security problem, not just a productivity one?
Every unsanctioned tool is an authentication gap and a potential data residency violation. When employees use consumer messaging apps because the corporate tool doesn't work well enough, the organization loses audit trail, data governance, and access control — all of which are compliance obligations in regulated industries.
How can IT leaders reduce the operational load of managing communication infrastructure?
Consolidating onto a unified communications platform reduces the number of vendor relationships, integration dependencies, and support surfaces to manage. Partnering with a managed service provider for ongoing operations, moves, adds, changes, upgrades, frees internal teams to focus on strategic work rather than routine maintenance.