How to Improve IT Vendor Management
How to improve IT vendor management across the full lifecycle — vendor inventory, tiering logic, contract protections, renewal strategy, and the operating model that makes governance repeatable at scale.

What Happens When IT Vendor Management Breaks Down
The signs are always the same. A renewal notice arrives 30 days before expiry. A security team flags a third-party tool that IT did not know was in production. A business unit cancels a license package three months after IT finished negotiating it. An audit finds data residency commitments in a contract that nobody has verified in two years.
None of these failures are dramatic. They accumulate quietly, and by the time leadership notices, the cost is already paid — in wasted spend, missed SLAs, or a compliance gap that survives until the worst possible moment.
IT vendor management is the structured practice of selecting, contracting, onboarding, governing, and offboarding external providers to deliver business outcomes with control and confidence. When it works, it cuts waste, reduces risk concentration, and gives IT leadership a defensible position in every budget conversation. When it does not, the vendor portfolio manages IT instead of the other way around.
This guide covers the full lifecycle, from building a vendor inventory when you do not have one to negotiating renewals with leverage. It is written for IT leaders who need vendor management that produces results, not paperwork.
Start Here: Build Your Vendor Inventory Before Anything Else
SaaS purchasing now happens across finance, HR, marketing, and individual engineers with corporate cards. By the time a tool reaches IT's radar, it may already be processing sensitive data, integrated into production systems, and auto-renewing annually. The vendor management lifecycle only works if the vendor register is accurate.
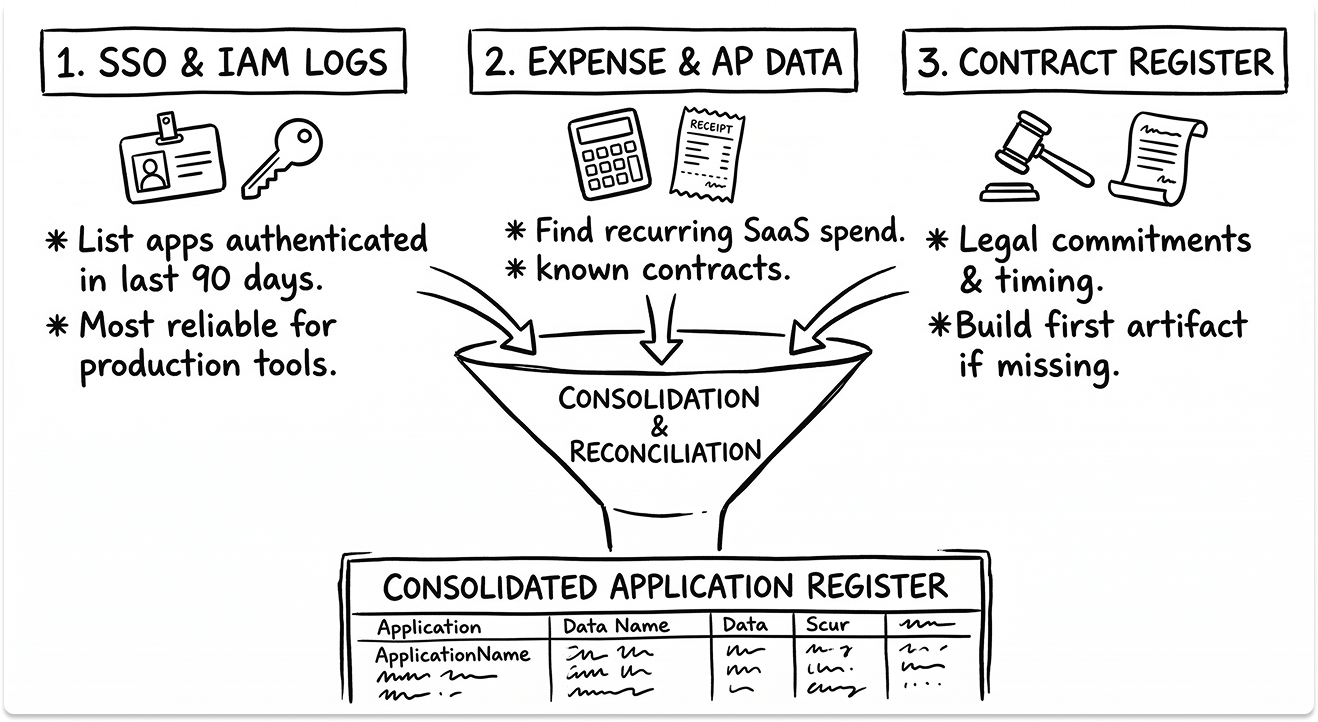
Start the inventory from three sources:
Your IAM and SSO logs show every application that authenticated against your identity provider in the last 90 days. This is your most reliable source for production tools. Anything not connected to SSO is either a governance gap or a shadow IT candidate.
Your expense reports and accounts payable data catch everything that bypasses IT procurement. Filter for recurring SaaS charges by vendor and cross-reference against your known contract register. The gap between these two lists is your shadow IT exposure.
Your contract register tells you what you are legally committed to and when. If you do not have one, this is the first artifact to build. At minimum, capture vendor name, business owner, data sensitivity classification, contract term, renewal date, and annual spend.
Once these three sources are reconciled, you have a working vendor register. Tag each vendor with inherent risk at intake. This becomes the foundation for tiering.
Vendor Tiering: The Decision That Scales Your Governance
Tiering is the most impactful efficiency decision in IT vendor management and the one most teams skip. Without it, every vendor receives the same oversight regardless of what they actually touch. A Tier 1 cloud infrastructure provider and a Tier 3 survey tool cannot receive identical governance investment without wasting your team's time on one and under-managing the other.
The tiering decision rests on four factors:
- Data sensitivity: Does this vendor process personal data, financial records, or regulated information? Does it have access to production systems or source code?
- Operational dependency: If this vendor went dark tomorrow, what breaks and how quickly? Is there a feasible substitute?
- Integration depth: How embedded is this vendor in your architecture? A vendor connected to five internal systems carries a different risk profile than a standalone tool.
- Spend concentration: High spend creates financial dependency and renewal leverage risk simultaneously.
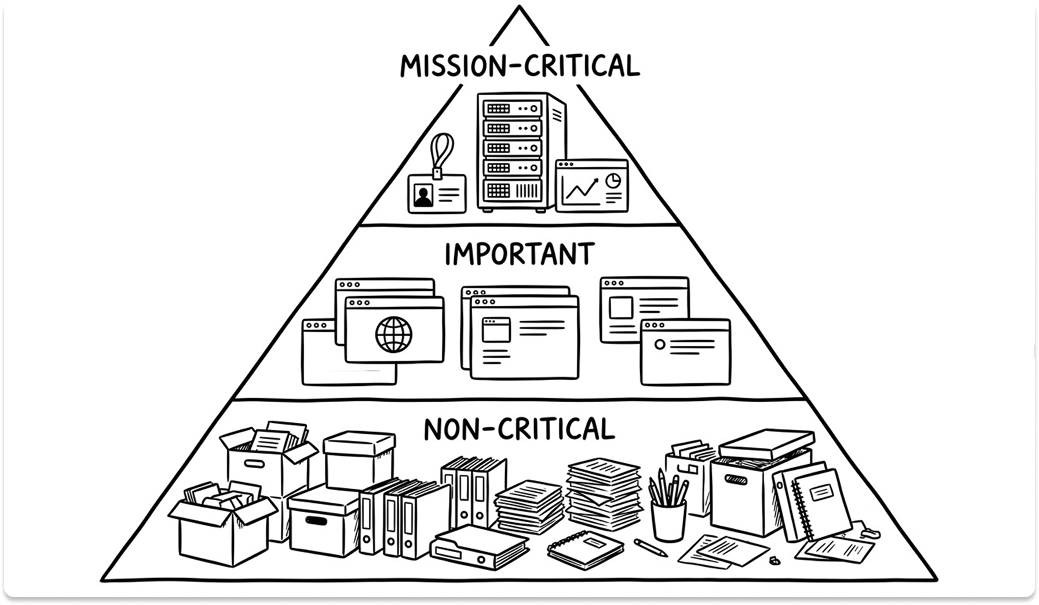
Tier 1 vendors are mission-critical. They process sensitive data, sit inside your production architecture, and have no near-term substitute. They require full due diligence, contractual SLAs with teeth, executive relationships on both sides, and quarterly business reviews. Your cloud providers, your core ITSM platform, and your identity infrastructure belong here.
Tier 2 vendors are important but not existential. They deliver material value, may process some sensitive data, and would take effort to replace. They warrant annual reviews, defined SLAs, and documented onboarding. Most of your business-unit SaaS tools live here.
Tier 3 vendors are non-critical. They are low-spend, low-risk, and replaceable. Manage them through standardized contracts, annual renewals with minimal review, and periodic portfolio rationalization to eliminate redundancy.
Tiering is not permanent. A vendor that starts as Tier 3 can migrate to Tier 1 as adoption deepens. Review tier assignments at every annual renewal and whenever a vendor's integration scope changes.
Sourcing and Evaluation: Anchor to Outcomes, Not Features
The most common sourcing failure in IT vendor management is entering an RFP without a defined success criteria. You evaluate dozens of capabilities and lose sight of the two or three outcomes the purchase needs to deliver.
Before any RFP is issued, document the problem statement, the target metrics that will confirm success, the must-have integrations, and the stakeholder who will own adoption. These four inputs are your evaluation anchor. Every vendor's response should be scored against them, not against a feature checklist that grows longer with every demo.
Run structured proof-of-value engagements, not open-ended pilots. A POV has a fixed timeframe, defined success criteria, a scoped data set, and a named decision owner. An open-ended pilot drifts, accumulates internal advocates, and ends with a decision made on momentum rather than evidence.
Weight your evaluation across four dimensions: business impact (does it solve the problem?), security and resilience (does it meet your risk threshold?), time-to-value (how quickly will it be adopted?), and total cost (license, implementation, ongoing, and exit). A vendor who scores highly on features but poorly on adoption readiness is a shelfware risk before the contract is signed.
Verify customer references in your industry. Ask specifically about support quality under pressure, not just during normal operations. And check the ecosystem: available connectors, marketplace terms, and API access determine how deeply you can integrate without incurring professional services costs you did not budget for.
Contract Management: Lock in Protections Before You Have Leverage
The negotiation window closes the moment the contract is signed. Everything your team forgot to ask for becomes a three-year problem or a costly amendment. This is where disciplined IT vendor management pays for itself most directly.
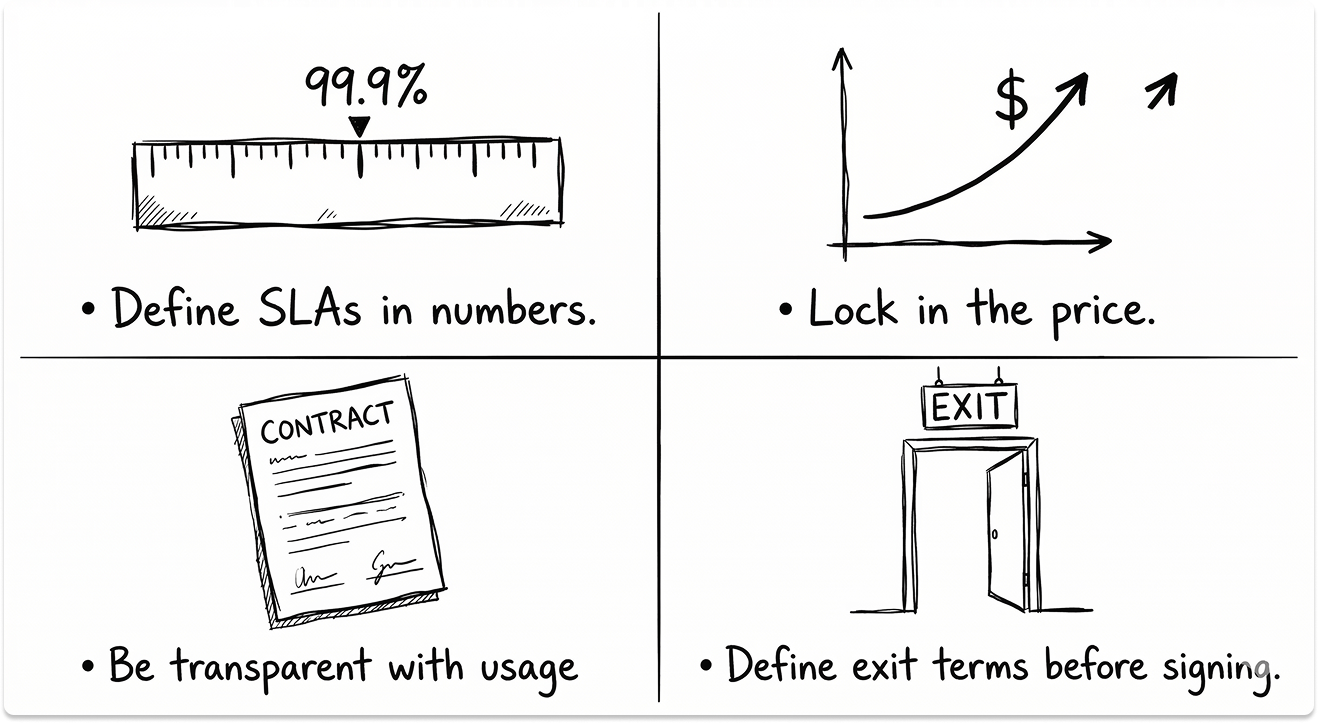
SLA definitions need numbers, not language. "High availability" means nothing. "99.9% uptime measured monthly with service credits of 10% of monthly fees per 0.1% below threshold" is enforceable. Define uptime math explicitly, set MTTR targets for critical incidents, and require vendor-provided reporting on SLA performance, not just a portal login where you have to pull it yourself.
Price protection belongs in the original contract. Annual increase caps, multi-year discount locks, and volume-tier structures are far easier to negotiate at signing than at renewal when your switching cost is visible to both sides. If a vendor refuses to cap annual increases, that is a negotiating data point worth capturing. It tells you how they will behave at renewal.
Usage audits and true-up rules determine whether SaaS spend stays predictable. Require contractual audit rights and define the true-up methodology. Without this, vendors can interpret usage in ways that generate unexpected invoices, particularly in consumption-based models.
The exit terms are as important as the entry terms. Specify data export formats and timelines, knowledge transfer requirements, integration teardown responsibilities, and deletion attestation procedures. For Tier 1 vendors, include transition assistance obligations and IP escrow provisions if the service underpins something irreplaceable. Negotiating these terms when a relationship is new is straightforward. Negotiating them when you are trying to leave is not.
Onboarding: Turn Contracts Into Outcomes
A contract signed is not value delivered. The gap between signature and measurable adoption is where most vendor investments fail to return what was promised.
Start with a technical review before any broad rollout. Validate the architecture against what was represented during evaluation. Confirm data flows, access controls, encryption configuration, SSO/MFA enforcement, and logging setup. Record these in your vendor management system so they are auditable and reproducible.
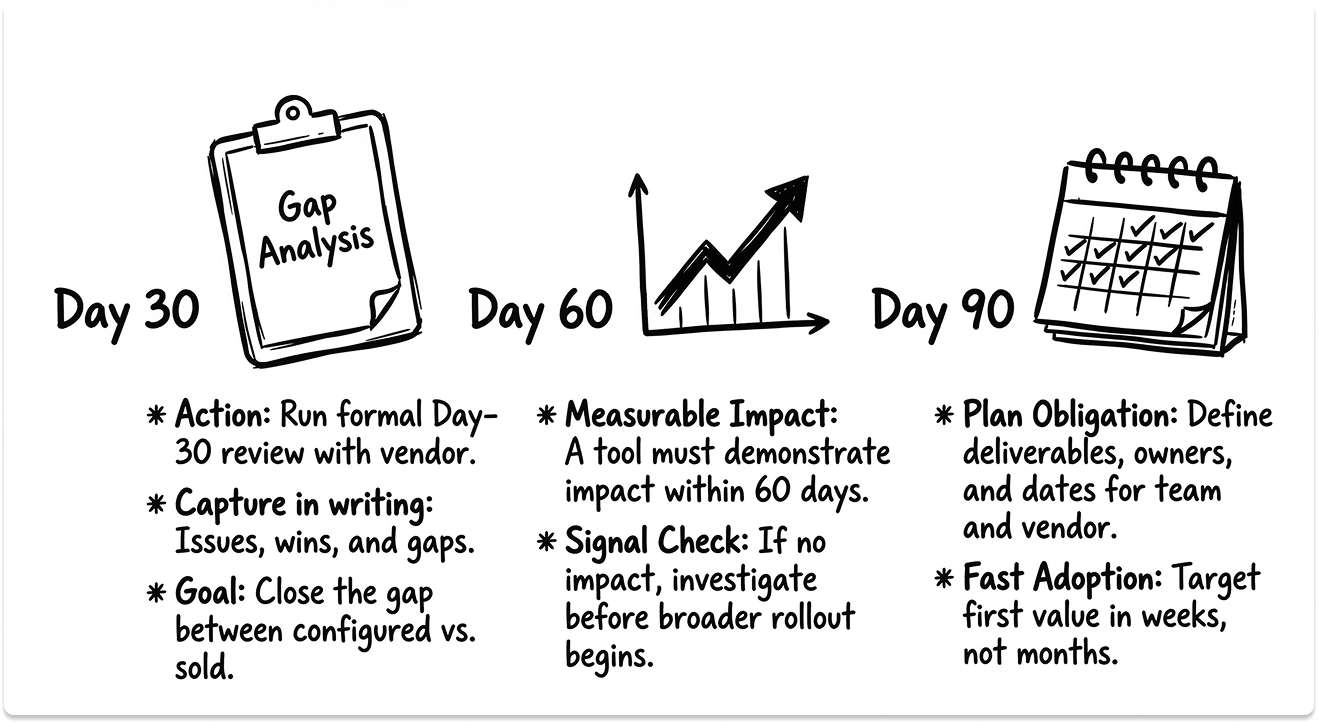
Define a 30/60/90-day plan with named deliverables, owners, and dates for both your team and the vendor. Target time-to-first-value in weeks, not months. If a tool cannot demonstrate measurable impact in the first 60 days, that is a signal worth investigating before a broader rollout locks in adoption inertia.
Track adoption KPIs from day one: active users as a percentage of licensed users, feature utilization rates, support ticket volume and resolution time, and automation rates if applicable. When these metrics live in your vendor management system, problems surface early when they are still fixable.
Run a formal day-30 review with the vendor's implementation team. Capture issues, wins, and gaps in writing. Close the gap between what was configured and what was sold. Most implementation problems are visible at day 30 and manageable at day 30. They become expensive at day 180.
Performance Management: Make QBRs Earn Their Calendar Slot
A quarterly business review that covers uptime and nothing else is a status call with slides. A QBR that drives decisions is different in structure and preparation.
Build a vendor scorecard that tracks four categories: SLA attainment (is the vendor delivering what was contracted?), adoption and utilization (is your organization extracting the value that justified the purchase?), incidents and MTTR (how does the vendor perform under pressure, not just under normal conditions?), and TCO versus benefits (is the cost-to-value relationship still defensible?).
Bring usage data, incident logs, and feature adoption metrics to every QBR. Vendors who know you arrive with data behave differently than vendors who expect a relationship conversation. The scorecard creates accountability without requiring confrontation.
Use QBRs to surface roadmap alignment early. Vendors with early-access programs and co-development relationships give you influence over product direction that has direct operational value. Push for executive sponsor alignment on both sides for Tier 1 vendors. Shared quarterly objectives and a visible risk log make the relationship a partnership rather than a transaction.
Tie chronic SLA misses and security gaps to service credits, remediation plans, or renewal risk. Document every corrective action with an owner and a due date in your vendor management system. Without this documentation, renewal conversations become subjective. With it, they are data-led.
Renewal Strategy: Start Earlier Than You Think You Need To
The most common renewal mistake is starting too late. When a renewal conversation begins 30 days before expiry, the vendor controls the negotiation. Your switching cost is visible, your timeline is compressed, and your alternatives are theoretical. Every piece of leverage you should have accumulated over the contract term becomes irrelevant.
Start your renewal process 180 to 270 days before the contract end date for Tier 1 and Tier 2 vendors. Use that time to build a decision memo that answers three questions: retain, optimize, or replace? Pull usage data, SLA history, incident records, support CSAT, and current business outcomes from your vendor management system. Data-backed renewals consistently produce better terms than relationship-based ones.
Eliminate waste before negotiating. Reclaim idle licenses, downgrade underused tiers, and remove overlapping tools before you present a renewal number. Walking into a renewal with a rationalized footprint signals that your team is informed and that inflated pricing will not survive a comparison to actual consumption.
Benchmark against the market. Fair market pricing for most enterprise software categories is publicly available through Gartner Digital Markets, Vendr, or Vertice. Know what peer organizations at similar scale are paying. If your vendor's renewal quote exceeds market rate, that is a specific and documentable negotiating position.
For usage-based and consumption models, negotiate true-up fairness clauses, overage caps, and audit rights. These models are designed to grow spend passively. The only protection is contractual.

AI in IT Vendor Management: Four Practical Applications Now
AI has entered vendor management at the operational level. The use cases that are mature enough to act on in 2025 are narrower than vendor marketing suggests, but they are real.
Automated evidence expiry tracking is the most immediately useful. Keeping SOC 2 reports, ISO 27001 certificates, and penetration test summaries current across a large vendor portfolio is a manual burden that AI-assisted platforms handle reliably. Tools like Vanta, Drata, and ServiceNow VRM can auto-flag expiring evidence and trigger reassessment workflows without manual calendar management.
AI-assisted security questionnaire responses compress due diligence cycles on both sides. If you are managing inbound questionnaires from customers, platforms like SafeBase and Conveyor maintain a live control library and auto-populate responses. If you are sending questionnaires to vendors, AI-assisted review can flag incomplete responses and surface inconsistencies before a human reviewer spends time on them.
Contract clause analysis has become practical for standard enterprise agreements. Tools like Ironclad and Luminance can scan vendor contracts for missing data protection provisions, non-standard liability caps, or problematic auto-renewal language faster than a legal review cycle. This does not replace legal review for complex agreements. It prepares the review by surfacing the issues worth human attention.
Usage anomaly detection identifies shelfware and over-provisioned licenses in real time rather than at renewal. SaaS management platforms including Zylo, Torii, and Productiv now embed this capability as a standard feature.
The Vendor Management Operating Model: Roles, Tools, and Accountability
IT vendor management at scale requires explicit ownership, not shared responsibility. Shared responsibility means no accountability when a renewal slips or a security review stalls.
Assign three named roles to every Tier 1 and Tier 2 vendor: a business owner who is accountable for adoption and outcome delivery, a technical owner who manages integration health and change management, and a risk owner who maintains due diligence currency and tracks compliance obligations. For Tier 3 vendors, a single business owner is sufficient.
Your vendor management office governs the lifecycle, maintains the standards, and holds the function accountable. Without a VMO or equivalent governance function, the lifecycle model exists on paper and breaks under pressure.
The tooling stack that makes this scalable covers four categories:
- Vendor management system or ITAM platform: centralized inventory, risk, contracts, and renewals (ServiceNow, Genuity, Zluri)
- CLM for contract control: clause libraries, approval workflows, and version control (Ironclad, Agiloft, Icertis)
- SaaS management platform: license hygiene, usage tracking, shadow IT detection (Zylo, Torii, Productiv)
- GRC or TPRM platform: risk scoring, evidence management, due diligence workflows (Vanta, OneTrust, ProcessUnity)
Automate the grind. Trigger renewal alerts 270, 180, and 90 days out. Auto-expire security evidence so reassessments happen on schedule. Flag dormant licenses for reclamation. Open tickets automatically when SLAs are missed. These are not configuration projects. They are the minimum viable automation layer that makes IT vendor management sustainable at scale.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is the first thing to fix in a broken IT vendor management program?
Build the vendor inventory. You cannot tier, govern, or negotiate a portfolio you cannot see. Start with IAM/SSO logs, expense reports, and your contract register. Reconcile them. The gaps between those three sources are your most urgent risk items.
How do you handle a vendor that consistently misses SLAs?
Document every miss in your vendor management system with timestamps and business impact. Trigger the service credit clause contractually, even if the amount is small. The act of invoking it creates a paper trail and signals that you are tracking performance seriously. If misses continue, use the documented history in your renewal negotiation as leverage for remediation plans, pricing adjustments, or a structured exit.
When does IT vendor management need a dedicated VMO?
When the portfolio exceeds 50 active vendors, when third-party risk is a regular audit finding, or when renewals are consistently managed reactively rather than proactively. A VMO does not require a large team. A function with clear mandate, documented standards, and a governance cadence can operate with two or three dedicated people. The alternative is distributing the work across people who have other primary jobs, which means it gets done when nothing else is urgent.
How do you get business units to follow vendor management intake processes?
Make the process faster than the alternative, not harder. A one-page intake form that returns a tiering decision and a pre-screened vendor shortlist in 48 hours competes successfully against the shadow purchasing that happens when IT procurement feels slow. The intake process succeeds when it helps business units buy faster and better, not when it creates a governance obstacle they route around.
What belongs in a vendor management dashboard for the CIO and CFO?
Four categories: risk (tier distribution, open findings, reassessment currency, breach notifications), performance (SLA attainment by tier, incident MTTR, support CSAT), value (adoption rates, license utilization, cost-to-value by vendor, shelfware reclaimed), and compliance (DPA status, data residency currency, audit findings open and closed). Update monthly. Review quarterly. Any metric that requires more than 30 seconds of explanation does not belong in an executive dashboard.