Tenable vs Qualys vs Rapid7: The IT Leader's Definitive Vulnerability Management Guide
A comparison of the three leading vulnerability management platforms — Tenable, Qualys, and Rapid7. Covers product lines, real-world performance, TCO, risk scoring, and how to make the right procurement decision for your environment.

The Problem With How Most Teams Pick a VM Platform
Vulnerability management platforms follow the same pattern for a decade. Security team shortlists three vendors. Vendors send decks. Procurement compares per-asset prices. Someone calls a reference. The contract goes to whoever lands the best deal on the final day of the quarter.
Six months later, half the assets are uncovered, the ServiceNow integration is a spreadsheet, and nobody can explain to the board what the risk score actually means.
The platform decision is not the hard part. Knowing precisely what you are evaluating and what questions to ask before the first demo is where most teams fall down. This guide cuts through that.
What You Are Actually Buying: The Product Line Problem
Each of the three vendors has deliberately blurred their product naming over the last three years as they extended from pure VM into broader exposure management platforms. Before comparing features, you need to know which product in each portfolio maps to an enterprise VM programme.
Tenable: Four Products, One Scanning Engine
Nessus Professional is a standalone scanner. It is not a VM programme. It produces point-in-time scan results with no remediation tracking, no asset criticality, and no continuous monitoring. At ~$6,790 per scanner per year, it is the right tool for consultants and pen testers. It is not the right tool for an enterprise security team running a continuous VM programme.
Tenable Vulnerability Management (formerly Tenable.io) is the cloud-managed enterprise platform. This is what most organisations buying "Tenable" are actually buying: continuous scanning, asset lifecycle tracking, VPR risk scoring, and remediation workflow integrations. Pricing runs from $30K to $500K+ per year depending on asset count and modules.
Tenable Security Center is the on-premises equivalent. Same scanning depth, full data residency control, higher operational overhead. The right choice for Federal agencies, air-gapped environments, and organisations with strict data sovereignty requirements. Budget at least 0.5 FTE to operate it effectively.
Tenable One is the full exposure management platform — VM plus external attack surface management, Active Directory risk, cloud security posture, and OT security in a single unified risk view. This is Tenable's Continuous Threat Exposure Management (CTEM) play. If your mandate extends beyond CVE management, this is the conversation to have.
Qualys: Cloud-Native Since Before It Was a Trend
Qualys has been cloud-native SaaS since 2000. That is a structural advantage that shows up in deployment speed, agent footprint, and operational overhead.
Qualys VMDR (Vulnerability Management, Detection, and Response) is the flagship. The critical differentiator is native patch management included in the base subscription. Neither Tenable VM nor Rapid7 InsightVM include patching natively, both route it through integrations. For organisations that want VM and patching in one platform without a second integration project, this matters.
Qualys TotalCloud extends VMDR into cloud security posture management (CSPM) for AWS, Azure, and GCP. Qualys EDR runs on the same Cloud Agent as VMDR without any agent deployment requirement. Both are add-ons to the base VMDR subscription.
Rapid7: The Insight Platform Bet
Nexpose is the legacy on-premises scanner. Rapid7 still sells and supports it, but they are actively steering customers toward InsightVM. If you are evaluating Rapid7 today, InsightVM is the product.
InsightVM is the cloud-managed enterprise VM platform. Its differentiator is the Real Risk Score — a prioritization model backed by live exploit data from Metasploit, the most widely used penetration testing framework in the world. When InsightVM scores a vulnerability as high-priority, it is because there is a working exploit in active use. That is a materially different signal than a CVSS score.
Exposure Command is Rapid7's CTEM play — aggregating InsightVM, InsightCloudSec, InsightAppSec, and threat intelligence into a unified exposure view. It is credible but less mature than Tenable One at the time of writing.
What Actually Matters in an Enterprise Evaluation
Vendor sales decks will show you feature parity across every category. The reality is more granular. Below are the criteria that determine whether or not does a platform delivers in production.
Plugin Library and Scan Depth
Tenable's plugin library exceeds 219,000 plugins — the largest of the three by a significant margin. In a heterogeneous enterprise environment with legacy systems, uncommon network devices, and OT assets alongside standard endpoints, coverage gaps are breach risk. This is the category where Tenable has maintained its lead for twenty years.
Qualys and Rapid7 both maintain large plugin libraries, but neither publishes precise numbers the way Tenable does. For environments running purely standard IT assets (Windows, Linux, cloud workloads, containers), the practical difference is small. For anything more complex, the coverage gap becomes material.
OT and ICS Support
Tenable is the market leader here and it is not close. Tenable OT Security (formerly Tenable.ot) provides passive monitoring and active scanning for industrial control systems, SCADA environments, and OT networks. It integrates natively with Tenable VM, giving a unified view of IT and OT risk in a single platform.
Neither Qualys nor Rapid7 has a credible OT offering at this depth. If your environment includes any operational technology, Tenable is effectively the only enterprise-grade VM platform in the conversation.
Risk Scoring: VPR vs. TruRisk vs. Real Risk
This is where the three vendors diverge most meaningfully and where the procurement conversation most commonly gets oversimplified.
CVSS (Common Vulnerability Scoring System) scores individual vulnerability severity. It does not account for whether a vulnerability is being actively exploited, whether your specific asset is internet-facing, or whether a working exploit exists in the wild. Sorting your patch backlog by CVSS 7+ in a typical enterprise environment gives you 8,000–100,000 items. That is not a prioritisation strategy.
According to CISA's Known Exploited Vulnerabilities catalog, of approximately 21,500 CVEs published in H1 2025, only 161 were being actively exploited in the wild by mid-year. That is 0.75% of total published CVEs.
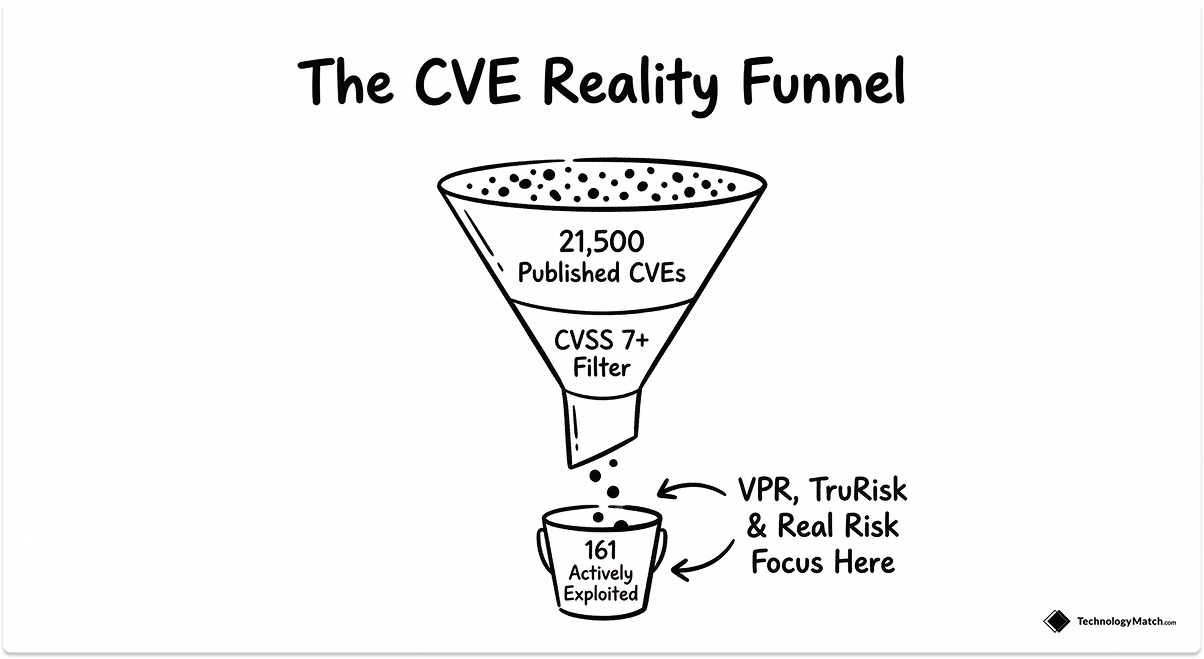
Tenable VPR (Vulnerability Priority Rating) incorporates threat intelligence, exploit code availability, and asset criticality into a daily-updated score. In Tenable's published customer data, VPR reduces the actionable patch list by 40–50% compared to raw CVSS sorting.
Qualys TruRisk produces a normalised 0–1,000 risk score that factors in business context, asset criticality, and real-world threat data. Its primary advantage is executive communication, a single number that non-technical stakeholders can track over time. For organisations where board-level security reporting is a priority, TruRisk is the most legible output of the three.
Rapid7 Real Risk Score is backed by live Metasploit exploit data. When a vulnerability scores high on Real Risk, it means the Rapid7 Labs team has observed active exploitation using Metasploit modules in real environments. For teams whose primary concern is "what can an attacker actually use against us today," this is the most operationally grounded signal of the three.
Native Patch Management
Qualys VMDR includes patch management in the base subscription. Tenable VM and Rapid7 InsightVM do not — both require integrations (typically with Microsoft SCCM, Ivanti, or dedicated patch tools via ServiceNow or Jira) to close the loop between vulnerability detection and remediation.
This matters operationally. Every integration is a failure point, a maintenance burden, and a potential source of remediation latency. If your organisation does not have a mature patch management toolchain already in place, Qualys VMDR's native capability eliminates an entire workstream.
If you already have a robust patching infrastructure and primarily need VM to feed it, the Qualys advantage disappears — and the comparison shifts to scan depth and risk scoring quality.
CTEM Readiness
Gartner introduced Continuous Threat Exposure Management as a framework in 2022. The core premise: vulnerability management alone is insufficient. Organisations need a continuous cycle of scoping, discovery, prioritisation, validation, and mobilisation across the full attack surface — not just CVE scanning.
Tenable One is the most complete CTEM-aligned platform available today. It unifies VM, external attack surface management, Active Directory risk (via Tenable Identity Exposure), cloud posture (via Tenable Cloud Security), and OT risk in a single exposure view. If building a CTEM programme is the mandate, Tenable One is the serious platform in the conversation.
Rapid7's Exposure Command is a credible second option, particularly for organisations already running InsightVM, InsightCloudSec, and InsightIDR. It aggregates across the Rapid7 Insight platform rather than building a purpose-built exposure management layer — an architectural difference worth understanding before committing.
Qualys is building toward CTEM via VMDR plus TotalCloud, but at the time of writing it lacks the identity exposure and EASM depth that Tenable One provides.
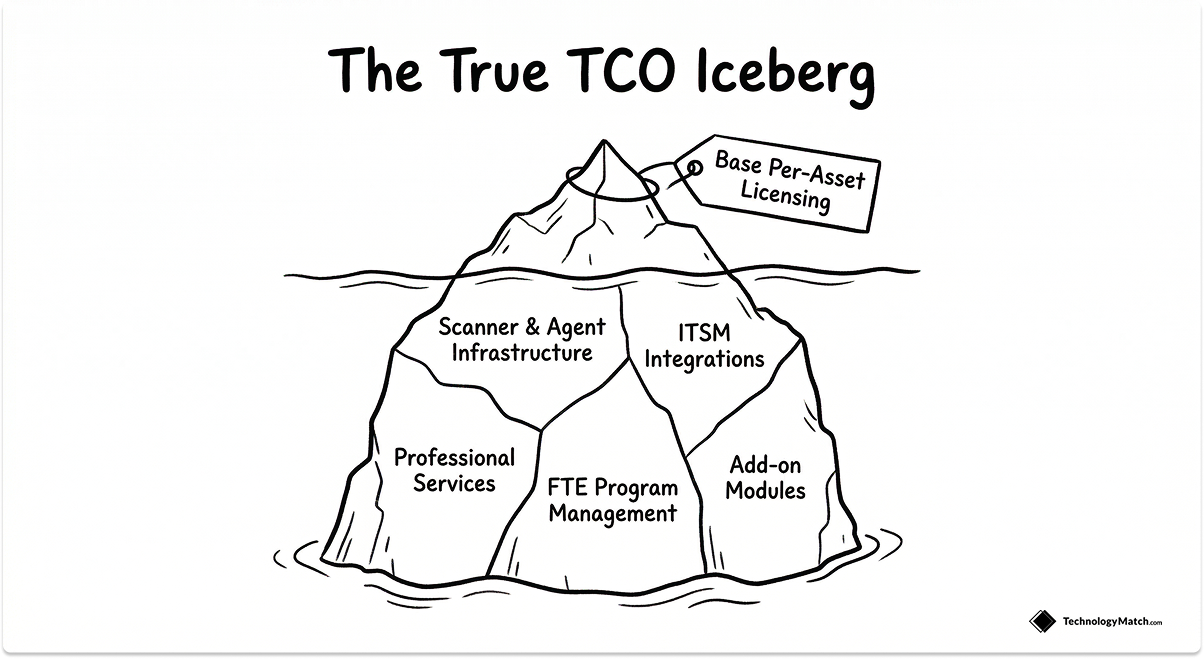
Total Cost of Ownership: The Number Vendors Don't Lead With
Per-asset licensing is the number that dominates VM procurement conversations. It is also the least useful number for understanding what a platform will actually cost over a three-year contract.
A realistic TCO model for an enterprise VM platform includes: base licensing, scanner and agent infrastructure, professional services for deployment and tuning, integration development (ServiceNow, Jira, SIEM), staff time for ongoing programme management, and add-on modules for capabilities not included in the base SKU.
Published per-asset pricing ranges (based on publicly available data and market research as of 2026) sit roughly as follows:
- Tenable VM: $26–$38 per asset per year at enterprise scale, cloud deployment
- Qualys VMDR: $17–$33 per asset per year, with patch management included in the base price
- Rapid7 InsightVM: ~$25–$35 per asset per year, the most transparent published pricing of the three
These ranges obscure more than they reveal. WAS (web application scanning), container scanning, EASM, and CTEM modules each add meaningfully to the base cost. An organisation licensing Tenable One with full module coverage is paying a materially different number than one licensing standalone Tenable VM.
The operational cost delta is equally significant. Tenable Security Center (on-premises) requires infrastructure investment and at least 0.5 FTE to operate. Qualys's cloud-native architecture eliminates that overhead entirely. For a 500-asset team, the infrastructure and staffing difference can dwarf the licensing delta.
Deployment and Integration Reality
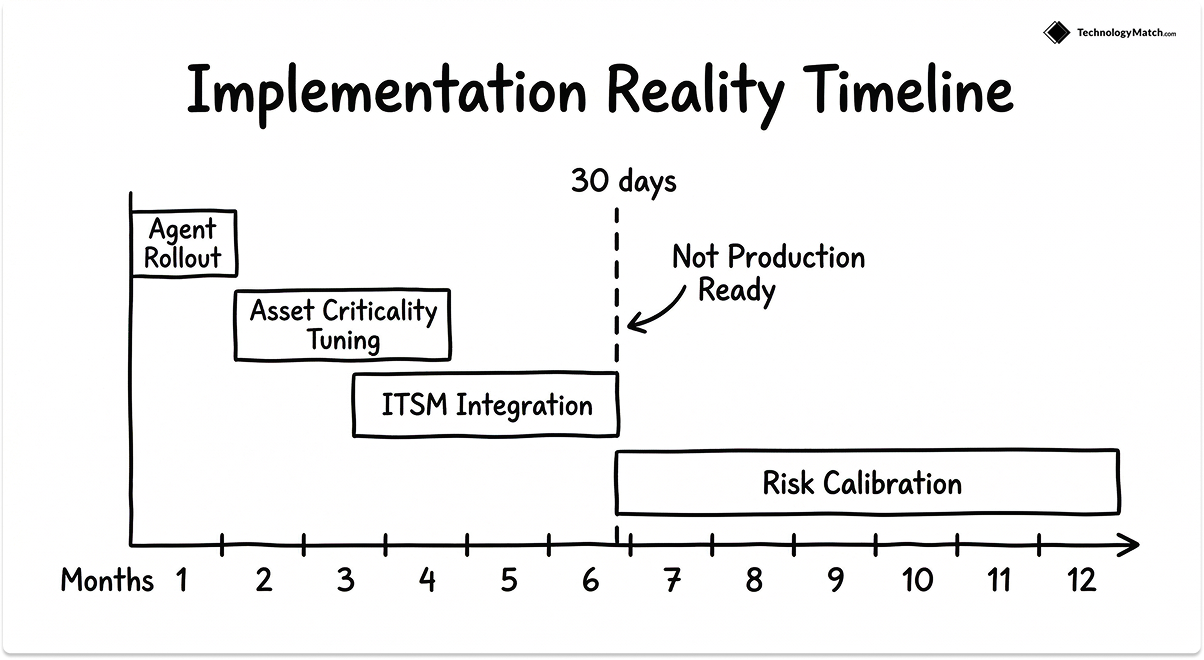
None of the three platforms are production-ready on day 30. A realistic deployment timeline for an enterprise VM programme looks like this:
- Months 1–2: Agent rollout, scanner placement, and initial scan coverage validation across the estate
- Months 2–4: Asset criticality configuration, scan policy tuning, and false positive triage
- Months 3–6: ITSM integration (ServiceNow or Jira), SLA definition, and remediation workflow testing
- Months 6–12: Risk scoring calibration, reporting standardisation, and executive dashboard build-out
Teams that expect a VM platform to deliver measurable risk reduction in the first quarter consistently underestimate the configuration and integration work. The platform is an engine, the programme is the vehicle. Both need to be built.
ServiceNow Integration
For organisations running ITSM on ServiceNow, Tenable has the most mature bidirectional integration of the three. Tenable's Security Center integration with ServiceNow Vulnerability Response is well-documented, widely deployed, and actively maintained. Qualys and Rapid7 both have ServiceNow integrations — neither matches Tenable's depth at enterprise scale based on peer review data from PeerSpot and Gartner Peer Insights.
Jira Integration
For DevOps teams running remediation through Jira, Rapid7's InsightVM integration is the strongest of the three. Rapid7's heritage in the developer security space gives it a natural advantage here — InsightVM's Jira connector is purpose-built for engineering-led remediation workflows rather than adapted from an ITSM-first architecture.
Read more: ITSM Tools Comparison: ServiceNow vs. Jira Service Management vs. Freshservice
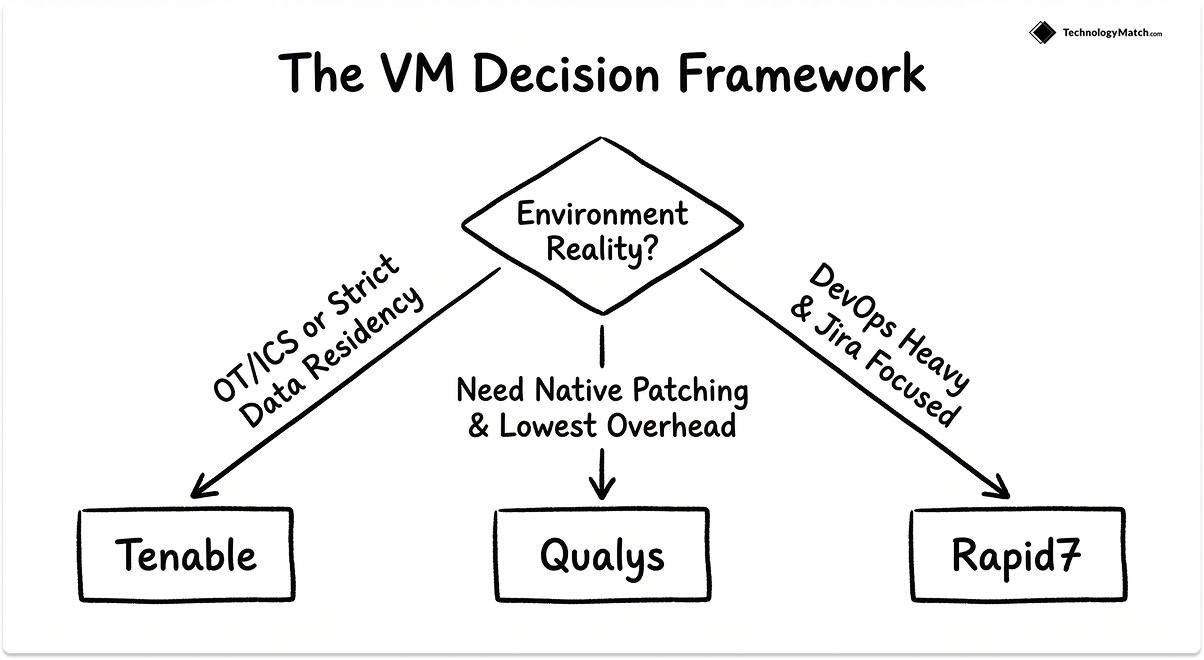
How to Pick: A Decision Framework
The right platform is the one that fits your environment, team, and programme maturity.
Here is how I think about the decision:
Choose Tenable VM or Tenable One if: your environment includes OT or ICS assets; you have a Federal mandate or strict data residency requirements; your primary ITSM tool is ServiceNow; or your mandate extends to a full CTEM programme and budget supports Tenable One.
Choose Qualys VMDR if: you want the lowest operational overhead of the three; you need native patch management without a separate integration project; cloud-native SaaS architecture is a hard requirement; or your board reporting requirements demand the clearest executive risk number (TruRisk).
Choose Rapid7 InsightVM if: your team runs remediation through Jira and DevOps workflows; you are already on the Rapid7 Insight platform (InsightIDR, InsightCloudSec); or you want the most operationally grounded prioritization signal; risk scores backed by real Metasploit exploit data rather than threat intelligence feeds.
When to Look Beyond These Three
If your estate is predominantly managed endpoints with CrowdStrike Falcon deployed, evaluate Falcon Spotlight before buying a net-new VM platform. It surfaces vulnerability data from the existing Falcon agent at materially lower marginal cost.
If you are running Microsoft Defender for Endpoint across a Windows-dominant estate with E5 licensing, Microsoft Defender Vulnerability Management is already available to you at near-zero incremental cost. It will not cover your full attack surface, but it eliminates the need for a dedicated VM platform for the covered assets.
Both options reduce vendor count and eliminate a second agent. The trade-off is narrower coverage and neither will catch your network devices, OT assets, unmanaged endpoints, or cloud-native workloads the way a dedicated VM platform does.
Due Diligence Before You Sign
Before committing to a multi-year VM platform contract, run through this checklist:
- Proof of concept on your actual estate. Not a demo environment. Run a 30-day PoC on a representative sample of your real assets — including your most complex asset types.
- Confirm module inclusions in writing. WAS, containers, cloud, OT, and identity exposure are commonly sold as separate SKUs. Get written confirmation of exactly what is included in your proposed contract before negotiating the price.
- Integration validation. If your remediation workflow runs through ServiceNow or Jira, test the specific integration version against your instance configuration. There is a material difference between a vendor saying they have a ServiceNow integration and that integration working correctly with your specific instance and version.
- Reference check on your asset profile. Ask for references from organisations with a similar mix of cloud, on-premises, remote endpoints, and OT assets. General enterprise references are less useful than ones that mirror your environment.
- Staffing model. Ask the vendor for their recommended staffing ratio for a programme your size. Any answer below 0.5 FTE for an enterprise deployment is underselling the operational requirement.
Closing Thoughts
Tenable, Qualys, and Rapid7 are all credible enterprise VM platforms. None of them is objectively "the best" — each has a set of conditions under which it outperforms the others.
Tenable has the broadest coverage and the most mature CTEM platform. Qualys has the lowest operational overhead and the only native patch management of the three. Rapid7 has the sharpest per-asset pricing at mid-market scale and the strongest DevOps-integrated remediation workflow.
The question is not which platform has the longest feature list. The question is which platform fits the environment you have, the team you have, and the programme you are trying to build. Get the answer to that right before you open a negotiation, and the rest of the procurement process becomes significantly easier.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is the difference between Tenable VM and Tenable One?
Tenable VM is the enterprise vulnerability management platform, continuous scanning, asset tracking, VPR risk scoring, and remediation workflow integrations. Tenable One is the full exposure management platform that bundles VM with external attack surface management, Active Directory risk (Tenable Identity Exposure), cloud security posture, and OT security in a single unified view. Tenable One is Tenable's answer to the Gartner CTEM framework. If your mandate is limited to CVE management across IT assets, Tenable VM is sufficient. If you are building a programme that covers your full attack surface including cloud, identity, and OT, Tenable One is the relevant product.
Is Qualys VMDR or Tenable VM better for compliance reporting?
Both platforms support the major compliance frameworks — PCI DSS, HIPAA, NIST, ISO 27001, FedRAMP, and DORA — with pre-built audit reports. Qualys has a slight edge for executive reporting because TruRisk produces a single normalised 0–1,000 score that non-technical stakeholders can track over time without requiring translation. Tenable Security Center has the edge for Federal and regulated environments that require on-premises data residency and FedRAMP Moderate authorization. The right answer depends on your compliance audience: board and C-suite communication favours Qualys TruRisk; Federal audit trail requirements favour Tenable Security Center.
How long does it take to deploy a VM platform and see results?
A realistic timeline for an enterprise VM deployment runs 6–12 months before the programme delivers consistent, actionable output. The first 60 days cover agent rollout and scanner placement. Months 2–4 focus on asset criticality configuration, scan policy tuning, and initial false positive triage. The ITSM integration, typically takes another 8–12 weeks to configure and test properly. Risk scoring calibration and executive reporting standardisation come last. Teams that expect production-ready output in the first quarter consistently underestimate the configuration work. None of these platforms are plug-and-play at enterprise scale.
Does Qualys VMDR include patch management?
Yes. Qualys Patch Management is included in the base VMDR subscription at no additional cost. This is a meaningful differentiator — neither Tenable VM nor Rapid7 InsightVM include patching natively. Both route patch deployment through integrations with tools like Microsoft SCCM, Ivanti, or ServiceNow Vulnerability Response. If your organisation does not already have a mature patching toolchain in place, the Qualys native capability eliminates an entire integration workstream and reduces the time between vulnerability detection and remediation.
What is the Real Risk Score in Rapid7 InsightVM?
The Real Risk Score is Rapid7's vulnerability prioritisation model, scored 0–1,000. Unlike CVSS, which scores individual vulnerability severity in isolation, Real Risk incorporates live exploit data from Metasploit, alongside asset exposure, vulnerability age, and malware kit availability. When InsightVM flags a vulnerability as high Real Risk, it means there is a working, actively used exploit available for it. For security teams whose primary question is what an attacker can actually weaponise against them today, Real Risk is the most operationally grounded prioritisation signal of the three vendors.
Which VM platform is best for OT and ICS environments?
Tenable, without qualification. Tenable OT Security (formerly Tenable.ot) provides both passive network monitoring and active scanning for industrial control systems, SCADA networks, and operational technology environments. It integrates natively with Tenable VM, giving security teams a unified view of IT and OT risk in a single platform and a single risk scoring model. Neither Qualys nor Rapid7 has a credible OT security offering at this depth. If your environment includes any operational technology, manufacturing plant floor, utilities infrastructure, building management systems, Tenable is effectively the only enterprise-grade VM platform in the evaluation.