What Tech Vendors Must Know About Data Protection in 2026
What enterprise buyers are actually asking about data protection, and what tech vendors need to have ready: certifications, trust centers, DORA readiness, AI transparency, and breach disclosure.

Data Protection Is Now the First Question, Not the Last
Security used to show up near the end of an enterprise deal, buried in a legal review. Today, it shows up in the first conversation.
According to a report, built on analysis of thousands of actual buyer-vendor interactions, found that more than half of B2B buyers raise security in their very first meeting with a vendor. That figure was 28% in 2023. It has nearly doubled in two years.
The reason is not hard to find. A 300% surge in SaaS-related breaches in 2024 forced procurement teams in healthcare, finance, and manufacturing to rethink how they evaluate vendors at the top of the funnel, not just the bottom.
By 2025, 93% of CISOs called SaaS security a top priority, and buyers arrived at discovery calls with security questionnaires already drafted.
If your sales team is still treating security as a legal formality to be handled after verbal commitment, you are losing deals you do not even know you lost.
The Buyer's Decision Logic Has Shifted
A study drawing on responses from over 2,600 organizations across 12 countries, put two numbers on the table that every vendor selling to enterprise buyers should print out and read.
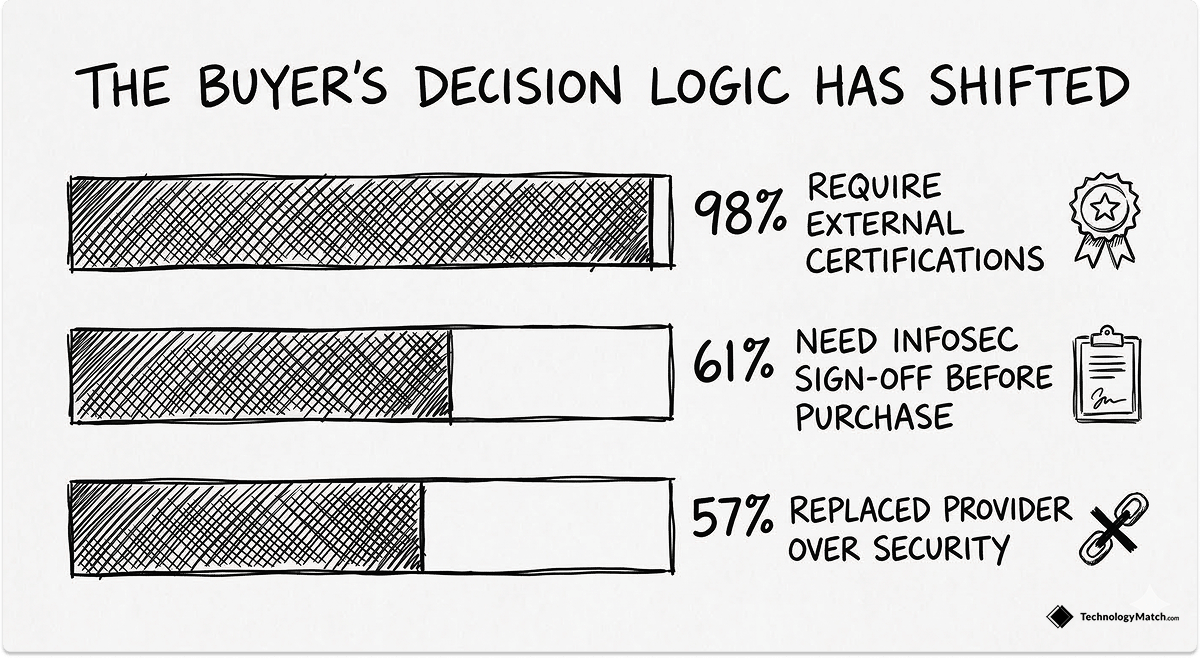
The first: 94% of respondents said their customers would not buy from them if they did not adequately protect data. The second: 98% said external privacy certifications are an important factor in their buying decisions, the highest level recorded in the study's history.
Those two statistics tell you something precise about the current market. Buyers are not just worried about data protection in the abstract. They are making purchasing decisions based on whether vendors can demonstrate it with verifiable, third-party evidence.
A verbal commitment, a policy document, or a completed questionnaire filled with "yes, we comply" answers is no longer sufficient.
And we know that there's behavioral proof to these survey findings. 52% of buyers now choose vendors based on certifications and data privacy posture. 57% replaced a SaaS provider specifically because of unresolved security issues. 61% of enterprise buyers require InfoSec sign-off before purchase, not after.
For tech vendors, this means security compliance is no longer a function of legal and IT. It is a revenue function.
Security Certifications: The Gatekeeper Has Changed
Why SOC 2 Is Now a Sales Prerequisite
Ten years ago, SOC 2 was a credential that differentiated you. Today, not having it disqualifies you.
According to another survey, 83% of enterprise buyers now require SOC 2 certification from SaaS vendors before signing contracts. Among companies with more than 5,000 employees, that figure rises to 91%.
The same survey found that 67% of startups that obtained SOC 2 reported it directly enabled them to close deals they would have otherwise lost, with a median deal size of $120,000 per deal. And according to Drata's 2025 State of Trust report, companies with SOC 2 Type II certification closed enterprise deals 35% faster than competitors without it.
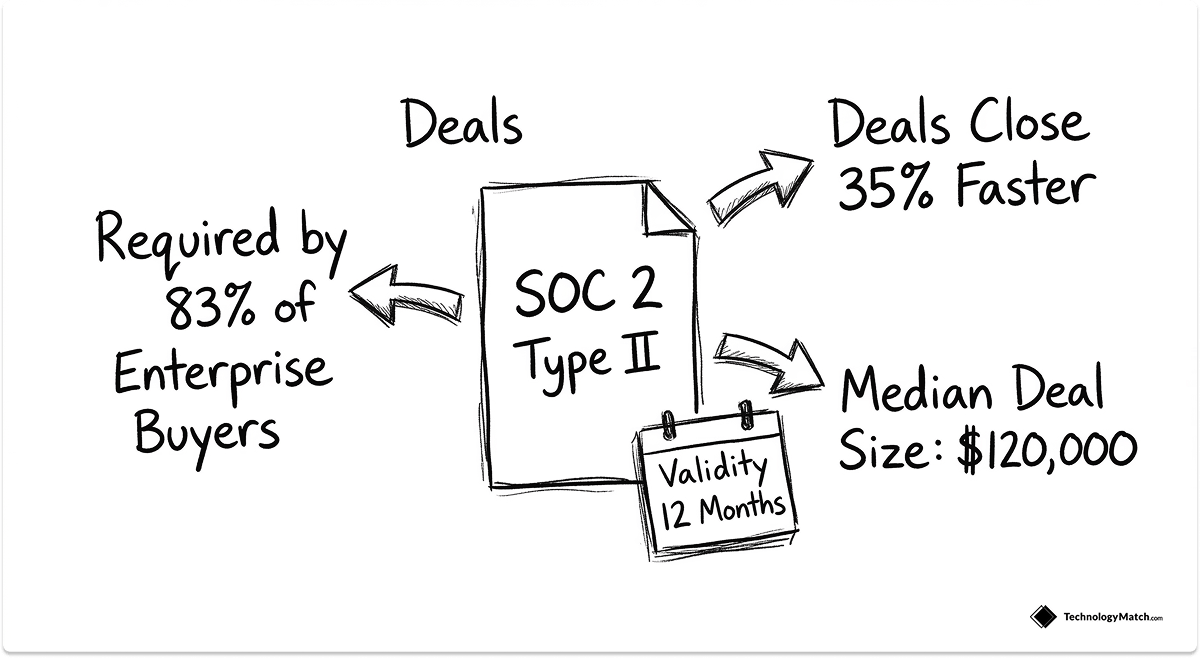
Gartner Digital Markets backs this up from the buyer side: 46% of software buyers prioritize security certifications and data privacy practices when choosing a vendor.
One practical illustration: In January 2025, a B2B SaaS startup was seven months into a $380,000 annual contract negotiation with a Fortune 500 company. The prospect's security team sent a 247-question vendor assessment.
SOC 2 is not a one-time achievement. The report is valid for 12 months and must be renewed continuously. A SOC 2 Type I report (point-in-time) runs $10,000 to $25,000. A SOC 2 Type II report (covering controls over a defined period, typically 6-12 months) runs $15,000 to $50,000. For any vendor with enterprise ambitions, this is a cost of sale, not overhead.
ISO 27001: The Credential That Opens EU and Global Enterprise Doors
SOC 2 dominates North American procurement. ISO 27001 handles everything else.
If you are selling into EU markets, regulated industries globally, government contracts, or large multinationals with complex supply chain standards, ISO 27001 is the credential that gets you onto the qualified vendor list. Vendors that hold it experience 40% faster vendor onboarding and 30% higher renewal rates compared to uncertified peers.
For SaaS companies pursuing enterprise deals in Europe or APAC, ISO 27001 often determines eligibility before any commercial conversation begins. Procurement portals in regulated industries screen for it before an RFP is even issued.
Which Certification to Pursue First
The answer depends on where your revenue is, or where you want it to be.
- North American enterprise buyers: SOC 2 Type II first. Get Type I within 3-4 months to unblock deals in the pipeline, then run a 6-month observation period toward Type II.
- EU/UK/APAC buyers, financial services, government: ISO 27001 first, or in parallel with SOC 2.
- Mature vendors with both markets: Carry both. The controls overlap significantly, and many compliance automation platforms now build both simultaneously.
The worst path is neither. Sprinto's analysis puts it plainly: 78% of enterprise clients now require SOC 2 Type II from their service providers. Without it, you are excluded from most enterprise deal flows before a sales conversation happens.
What Security Due Diligence Actually Looks Like in 2026
Understanding what buyers are doing during vendor due diligence matters more than understanding why they care.
The security review process now typically covers five domains:
- Data handling and encryption: Is data encrypted in transit and at rest? What algorithm? Who controls the encryption keys? What is the key rotation schedule?
- Access management: How is privileged access controlled? Is MFA enforced? Do you use SSO/SAML? Does your access model follow least privilege?
- Incident response: What is your breach notification timeline? Who is the incident commander? What is the escalation chain? Can you provide a documented IR plan?
- Third-party and fourth-party risk: Who are your subprocessors? How do you assess your vendors' security? Do you have a subprocessor list?
- Compliance and certifications: SOC 2 Type II report (actual report, not a certificate image). ISO 27001 certificate. Penetration test results from the past 12 months. Evidence of remediation on findings.
The critical word in that last point is evidence, not attestation. Buyers are no longer accepting "yes, we conduct annual penetration testing" as an answer. They want the test report, the finding severity breakdown, and documented proof that critical and high findings were remediated within stated SLAs.
Missing security documentation packets add 26% to sales cycles. Each round trip where a prospect asks for something you don't have ready, and you spend two weeks finding and preparing it, costs you a month of deal cycle time. Across a 6-month enterprise sales cycle, that kind of friction turns into lost deals.
Buyers are also now running backchannel reference checks on a vendor's past incident response. How a vendor handled a previous breach matters as much as whether they had one. More on this below.
Your Trust Center Is a Sales Asset, Not a Compliance Document
A trust center is a public or gated web portal where you publish your security documentation in a structured, always-current format. It is not a PDF folder. It is not a shared Google Drive link. It is a living security profile that buyers can access during evaluation without asking your sales team for anything.
Trust centers cut conversion time by 32%. When procurement teams, legal reviewers, and CISOs can access your SOC 2 report, penetration test executive summary, DPA template, subprocessor list, and incident response framework on demand, the security review becomes a parallel track rather than a sequential blocker.

A trust center typically contains:
- SOC 2 Type II report (full report or executive summary, gated under NDA)com
- ISO 27001 certificate with scope statement
- Penetration test executive summary (most recent, dated)
- Data Processing Agreement (DPA) template
- Subprocessor list with data locations
- Incident Response Plan (summary)
- Data residency and storage location documentation
- Uptime and availability history
- Security policies summary (access control, encryption, change management)
The operational difference is significant. Without a trust center, every security questionnaire triggers a manual process: find the document, confirm it's current, get legal approval to share, wait for NDA execution, send via email.
With a trust center, the buyer accesses it immediately, self-serves 80% of their questions, and your security team handles only the edge cases.
Companies like Segment have made "it's all public, here's the link" a standard response to vendor security inquiries. The result is measurably faster deal cycles, in some documented cases cut by 50%.
DORA and NIS2: What Non-EU Vendors Get Wrong
If you sell to EU financial institutions, EU critical infrastructure, or any EU-regulated entity, your data protection posture is now subject to two frameworks that most non-EU vendors are only beginning to understand.
DORA (Digital Operational Resilience Act) entered full force on January 17, 2025. It covers banks, insurers, investment firms, payment institutions, and fintech companies across all EU member states, and their ICT vendors.
This last point is the one vendors miss: DORA applies to you regardless of where you are headquartered, if you supply ICT services to EU financial entities. A US-based cloud provider serving European banks is in scope.
DORA's third-party requirements for ICT vendors are specific. Your contracts with EU financial entity clients must now include: defined service level agreements with measurable performance criteria, explicit data location and access rights, audit rights granted to the client and to regulators, documented exit and termination provisions, and breach notification timelines in hours, not days.
NIS2 applies more broadly, covering 18 critical sectors including energy, health, transport, digital infrastructure, and managed IT services. NIS2 penalties for non-compliance reach up to €10 million or 2% of global annual turnover, and personal liability for senior executives applies in cases of negligence.
For ICT vendors serving NIS2-covered sectors, supply chain risk management requirements cascade: your clients are required to assess and document your security posture, and they will ask for evidence, not policies.
The practical implication for vendors: if you are selling into EU markets, your security compliance documentation needs to be prepared at a level that survives regulatory scrutiny of your client's audit, not just a commercial procurement review.
Standard North American contract templates frequently conflict with DORA and NIS2 requirements on audit rights, data residency, and exit provisions. Prepare EU-specific contract addenda and have them ready before the deal reaches legal.
AI Vendors: A New Category of Buyer Scrutiny
If your product uses AI, your data protection conversation has a new, distinct dimension that standard security reviews do not cover.
The central buyer concern with AI vendors is training data: does using your product mean your model trains on their data? This question has become a qualification-stage filter, not a due diligence detail. Buyers are asking it in the first meeting, and an unclear or hedged answer frequently ends the evaluation.

A study found that 91% of businesses recognize they need to do more to reassure customers that their data is used only for intended and legitimate purposes in AI applications.
48% admitted that employees were entering non-public company information into GenAI tools. The buyer-side anxiety about data leaking into AI training pipelines is acute, and justified.
Questions buyers now ask AI vendors that fall outside standard security reviews:
- Does our data train your model? Under what conditions, and how do we opt out?
- Where are embeddings and vector representations of our data stored?
- Who are your AI subprocessors (model providers, fine-tuning vendors, infrastructure)?
- Do you conduct Data Protection Impact Assessments (DPIAs) for AI features?
- Can you provide a model card or training data documentation?
- What is your model update cadence, and how are customers notified of changes that affect data handling?
If you cannot answer these questions clearly and in writing, you will lose deals to competitors who can. The EU AI Act begins full application in August 2026, adding a regulatory layer on top of existing GDPR obligations for AI systems. Vendors should treat AI-specific transparency documentation as a product requirement for EU market access, not an optional add-on.
The practical preparation is a short AI transparency pack: a one-page document per AI feature explaining training data sourcing, inference data handling, customer data isolation practices, and opt-out mechanisms. Many enterprise legal teams are now requesting these before DPA negotiation begins.
Contract Terms Buyers Are Negotiating for Data Protection
The contract review stage is where vendors encounter buyers' most specific and non-negotiable data protection requirements. Being unprepared at this stage adds weeks to deal cycles and sometimes kills deals that were otherwise closed.

The terms buyers now routinely push for in enterprise data protection contracts:
Breach notification timelines. GDPR requires 72-hour notification to data protection authorities. NIS2 requires initial notification within 24 hours. Many enterprise legal teams now push for contractual commitments that match or exceed these timelines. "We will notify you promptly" is no longer acceptable language.
Audit rights. Regulated industries and DORA-covered entities require the right to audit vendor security controls directly, or to receive third-party audit reports on demand. If your contract limits audit rights, expect this to become a point of negotiation for every EU financial client.
Data Processing Agreements. Having a pre-drafted, GDPR-compliant DPA template ready to share at the start of legal review cuts weeks off the contract cycle. If every deal requires a DPA to be negotiated from scratch, you are adding unnecessary cost and delay. Build a standard DPA template and have your legal team review it annually.
Data return and destruction provisions. Buyers want contractual assurance that their data is returned in a usable format and certifiably destroyed within a defined period after contract termination. This is standard in enterprise SaaS contracts and should not require negotiation.
Cyber liability insurance. Enterprise buyers are increasingly requiring vendors to carry cyber liability insurance with minimum coverage thresholds, commonly $5 million. Know your policy limits before entering procurement discussions.
Vendors who arrive at legal review with pre-prepared DPA templates, clear liability positions, documented IR processes, and standard data protection addenda close contracts faster. The security conversation is already over. Legal is just documenting what has already been established.
If You Have Had a Breach: How to Handle It During a Sales Cycle
This is the topic no vendor wants to discuss and the one buyers are actively researching.
Backchannel reference checks now routinely include questions about a vendor's past incidents. Procurement teams search news archives, threat intelligence feeds, and industry forums before shortlisting vendors. If you have had a breach and buyers discover it from a news article rather than from you, the deal is almost certainly over.
The counterintuitive truth is that a disclosed breach handled well can actually build trust, and I have seen this play out in practice. Buyers know that no organization is immune to incidents. What they are evaluating is whether your incident response is mature, your communication is transparent, and your remediation was thorough. A vendor who proactively discloses a past incident, explains what happened, describes the containment and remediation steps, and shows evidence of the controls put in place afterward is demonstrating exactly the security maturity buyers want.
The practical approach if you are currently in a deal and have a breach history:
- Disclose it before they find it. Brief your champion and offer a direct briefing with your CISO or security lead for the prospect's security team.
- Lead with remediation, not apology. Buyers want to know what changed, not how sorry you are. Prepare a one-page incident summary: what happened, timeline, root cause, containment actions, and systemic controls added.
- Offer references from clients who stayed. A client who remained with you through an incident and can speak to your response is your most credible security reference.
What ends deals is not the breach itself. It is the discovery that the vendor minimized, delayed disclosure, or left gaps in remediation that remain unaddressed. Transparency at disclosure is the only viable strategy.
The Vendor Data Protection Playbook: Sequenced by Stage
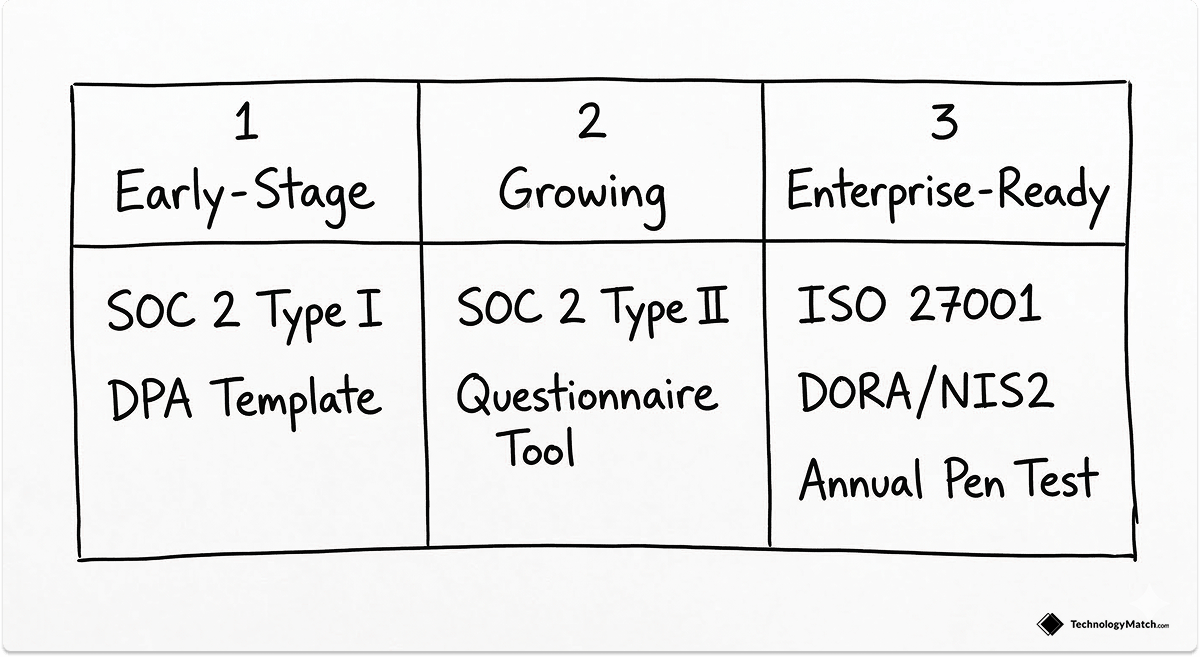
Early-Stage Vendor (Pre-Series A / First Enterprise Deals)
- Get SOC 2 Type I within 4 months (unblocks most mid-market deals)
- Build a security response kit: documented policies, encryption standards, IR plan, MFA enforcement confirmation
- Register a basic trust center page with your current policies and compliance status
- Draft a DPA template with legal counsel
Cost estimate: $15,000-$40,000 in compliance tooling and audit fees. Recoverable in the first enterprise deal it enables.
Growing Vendor (Series A / Active Enterprise Pipeline)
- Complete SOC 2 Type II with a 6-12 month observation period
- Begin ISO 27001 gap assessment if EU deals are in the pipeline
- Upgrade trust center to include gated document sharing with NDA automation
- Implement a security questionnaire response library (tools like Vanta, Drata, or SafeBase)
- Prepare EU-specific DPA addendum covering GDPR Article 28 requirements
Milestone: When 61% of your enterprise deals require InfoSec sign-off, your security team needs to be a structured part of the sales motion, not a reactive interrupt.
Enterprise-Ready Vendor (Series B and Beyond / EU Market Entry)
- Maintain SOC 2 Type II with continuous monitoring
- Achieve ISO 27001 certification
- Complete DORA readiness assessment if selling to EU financial entities
- Prepare NIS2 supply chain documentation for EU critical infrastructure clients
- Build an AI transparency pack if any product features use AI
- Establish a penetration testing cadence (at minimum annual; quarterly for high-risk categories)
- Assign a dedicated security sales engineer or solution architect for enterprise deals
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
Do I need both SOC 2 and ISO 27001?
Probably, if you sell into both North American and EU enterprise markets. SOC 2 is the de facto standard in US procurement. ISO 27001 is expected for EU buyers, regulated industries globally, and large multinationals. The controls overlap significantly, and most compliance automation platforms build both simultaneously. Running them in parallel costs roughly 20-30% more than sequential certification but gets you to full market coverage 12-18 months faster.
What is the biggest security review mistake vendors make?
Treating it reactively. The average enterprise security questionnaire contains 200-400 questions and requires input from engineering, legal, IT, and compliance. When that questionnaire arrives while a deal is in negotiation, most vendors spend 3-6 weeks pulling a response together, stalling the deal at the worst possible moment. Build your security response library before you need it, keep it current, and designate a single owner. That one change compresses review cycles from weeks to days.
How do I handle a 1,000-question security questionnaire?
You don't fill it out manually. Security questionnaire automation platforms, including Vanta, Drata, SafeBase, and Conveyor, maintain a master library of your security controls and use AI to map them to incoming questionnaire questions. For high-volume vendors, this reduces response time from weeks to hours. The first thing to do is build your master control library accurately. Everything downstream depends on that single source of truth.
What should a data processing agreement cover?
At minimum: purpose and scope of processing, categories of data processed, sub-processor list with locations, security measures required, breach notification timeline and process, data subject request handling, audit rights, data retention period, and data return or destruction obligations on termination. For GDPR-covered processing, the DPA must also address the lawful basis for any international data transfers. Have a standard template reviewed by EU-qualified counsel. Sending a bespoke DPA to every prospect is avoidable and expensive.
Does having a past breach disqualify me from enterprise deals?
No, but hiding it will. Enterprise buyers, especially in regulated industries, run incident history checks as part of vendor due diligence. A breach that was disclosed promptly, contained quickly, and remediated with documented controls is recoverable. A breach discovered from a press release after you said nothing is not. If you have a breach history, prepare a clear incident summary and have it ready to share proactively.





