Proofpoint vs Mimecast vs Abnormal Security: Email Security Comparison Guide for IT Leaders (2026)
Compare Proofpoint, Mimecast, and Abnormal Security on architecture, BEC detection, deployment complexity, and pricing. A vendor-neutral breakdown for IT leaders evaluating email security in 2026.
Why Your Email Security Decision Matters More Than You Think
Business email compromise (BEC) cost organisations $2.9 billion in reported losses in 2023, according to the FBI's Internet Crime Complaint Center. That is more than ransomware, more than data breaches, and more than any other cybercrime category the IC3 tracks. The median loss per BEC incident is over $50,000.
The attacks that cause those losses are not caught by spam filters or attachment scanners. They are plain-text emails that look exactly like a message from your CFO, your law firm, or your largest vendor.
That context matters when you are choosing between Proofpoint, Mimecast, and Abnormal Security. These are not interchangeable products solving the same problem with different interfaces. They represent three different architectural philosophies about how to stop email-borne threats. The architecture you choose determines which attacks you catch and which ones land in your executive's inbox.
The Three Architectural Models
Understanding the architectural difference between these platforms is the most important thing you can do before evaluating them.
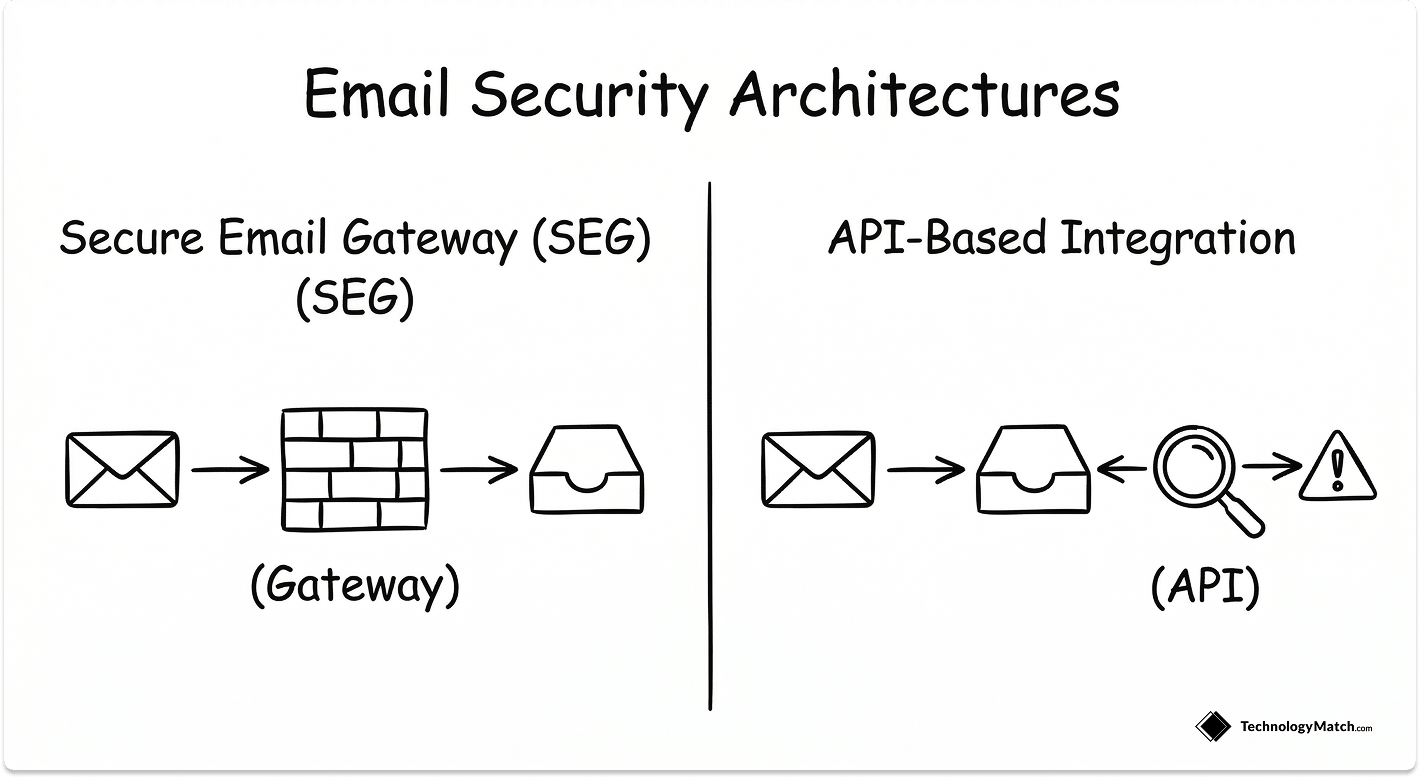
Proofpoint and Mimecast are Secure Email Gateways (SEGs). They sit in front of your email environment. Traffic routes through their infrastructure before it reaches your mail server. They inspect every message against known threat signatures, URL reputation databases, sandbox environments for attachments, and AI models trained on threat intelligence.
The SEG model is proven, mature, and effective against the threats it was designed to catch.
Abnormal Security is an API-based platform. It does not sit in your mail flow at all. It connects to Microsoft 365 or Google Workspace via API, reads your historical email data to build a behavioural baseline for every user and vendor relationship, and flags anomalies in real time.
It does not replace your email gateway. It is designed to catch what the gateway misses.
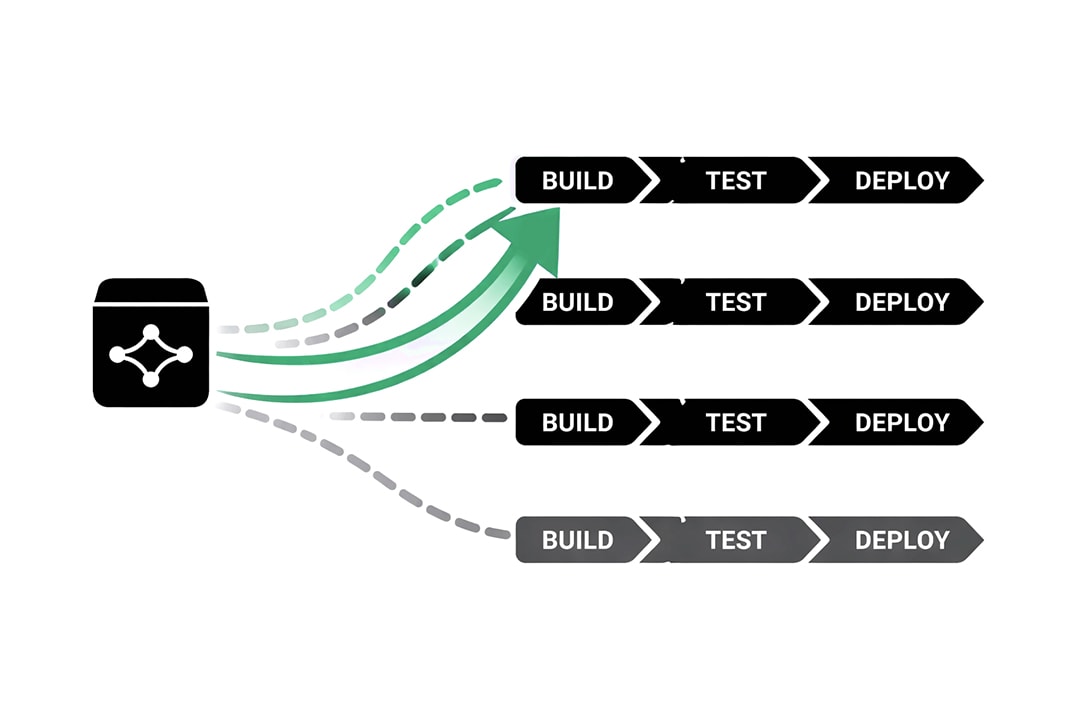
This architectural difference has direct operational consequences:
- SEGs require MX record changes and mail flow reconfiguration to deploy. Abnormal deploys in hours with no MX changes.
- SEGs block threats before delivery. Abnormal detects and remediates after delivery. It can pull messages from inboxes automatically, but the email technically arrives first.
- SEGs are effective against known threat types. Abnormal is designed specifically for novel, text-only, socially engineered attacks with no malicious payload to scan.
Neither model is superior in absolute terms. The right architecture depends on what you are trying to stop.
Proofpoint: Deep Coverage for Threat-Heavy Environments
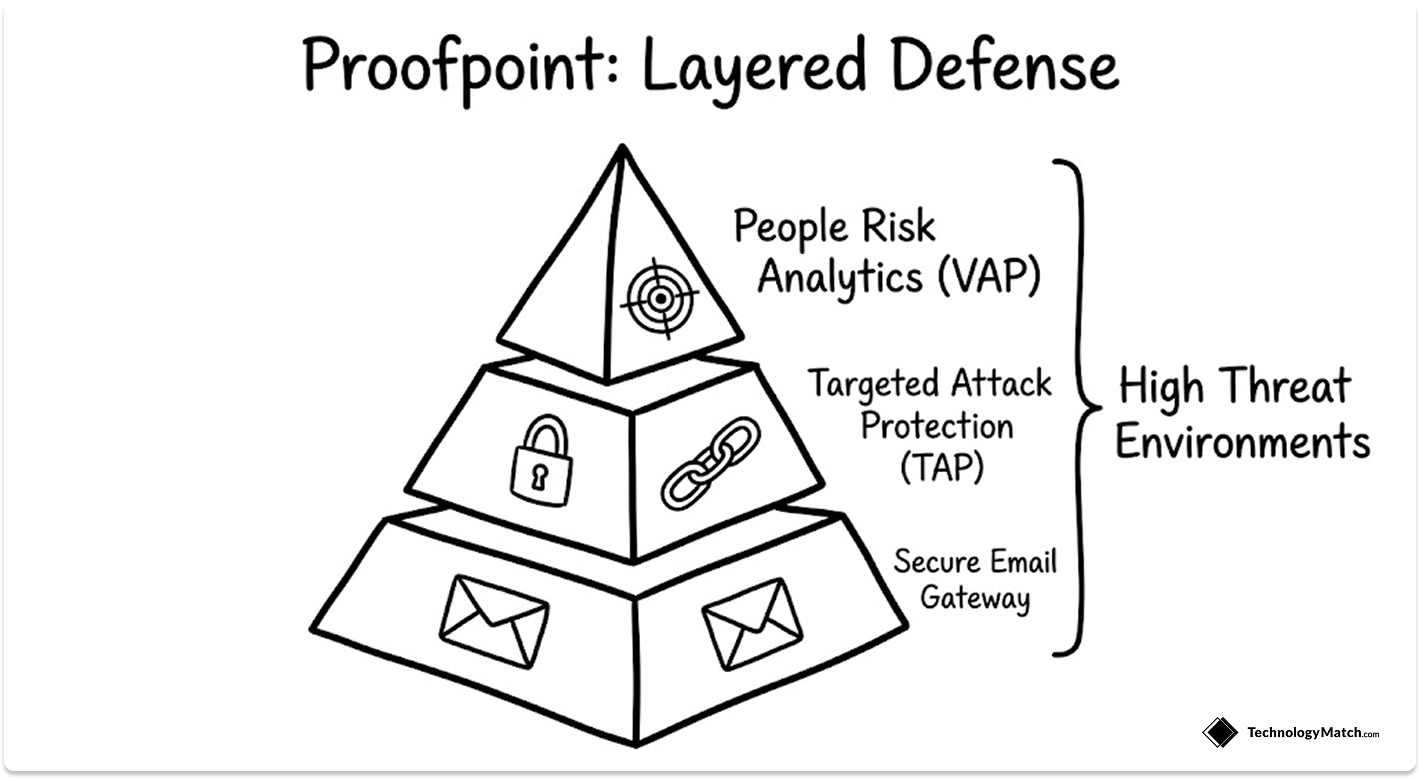
Proofpoint is the market leader in enterprise email security by revenue and deployment breadth. Its core platform, Proofpoint Threat Protection, combines a secure email gateway with URL defence, attachment sandboxing, BEC detection, and a people-centric risk layer called Nexus People Risk Explorer.
Nexus identifies your most attacked, most vulnerable, and most privileged users. For security teams running structured vendor management KPI frameworks, this people-risk data feeds directly into how you prioritise controls and training investment.
Where Proofpoint is Strongest
URL and attachment defence. Proofpoint's TAP (Targeted Attack Protection) rewrites every URL in every email and detonates every attachment in a sandbox before delivery. Its threat intelligence database is one of the largest in the industry. The company processes over 2.6 trillion messages annually, giving its detection models more signal than almost any competitor.
People-centric risk visibility. Proofpoint's VAP (Very Attacked People) reporting identifies which individuals in your organisation are receiving the most targeted attacks.
This is operationally valuable. It tells you where to focus security awareness training budgets, where to apply stricter controls, and which accounts represent the highest risk if compromised. For organisations building out a formal security posture, this connects directly to your IT vendor compliance framework.
Compliance and archiving. Proofpoint has a mature DLP and archiving stack that integrates with its email security layer. For regulated industries, having threat protection and compliance archiving from one vendor reduces integration complexity. If you are evaluating vendors for compliance-heavy environments, the guidance in our IT vendor evaluation for HIPAA and SOC 2 article applies directly here.
Threat intelligence breadth. Proofpoint's research team publishes some of the most cited threat intelligence in the industry. That research feeds directly into their detection models and is updated continuously based on live threat data.
Where Proofpoint Falls Short
Proofpoint is not a simple product to operate. The administrative interface has improved over recent years but remains complex, particularly for teams managing multiple tenants or large policy sets.
Support quality below enterprise tier is inconsistent. Smaller deployments frequently report difficulty reaching engineers with real product knowledge.
Pricing scales significantly with add-ons. The base threat protection tier handles gateway filtering, but the capabilities that make Proofpoint genuinely differentiated, TAP, CASB integration, and people risk analytics, are all higher-tier SKUs.
Pricing: Starts at approximately $30 to $50 per user per year for base protection. Enterprise tiers with TAP and advanced analytics run significantly higher. Proofpoint does not publish list pricing publicly.
Best for: Enterprises with a dedicated security team, a complex threat environment, and a need for integrated DLP and compliance capabilities alongside email threat protection.
Mimecast: Operational Simplicity and Total Cost of Ownership
Mimecast's pitch is different from Proofpoint's. Where Proofpoint leads with threat intelligence depth, Mimecast leads with operational simplicity, total cost of ownership, and email continuity.
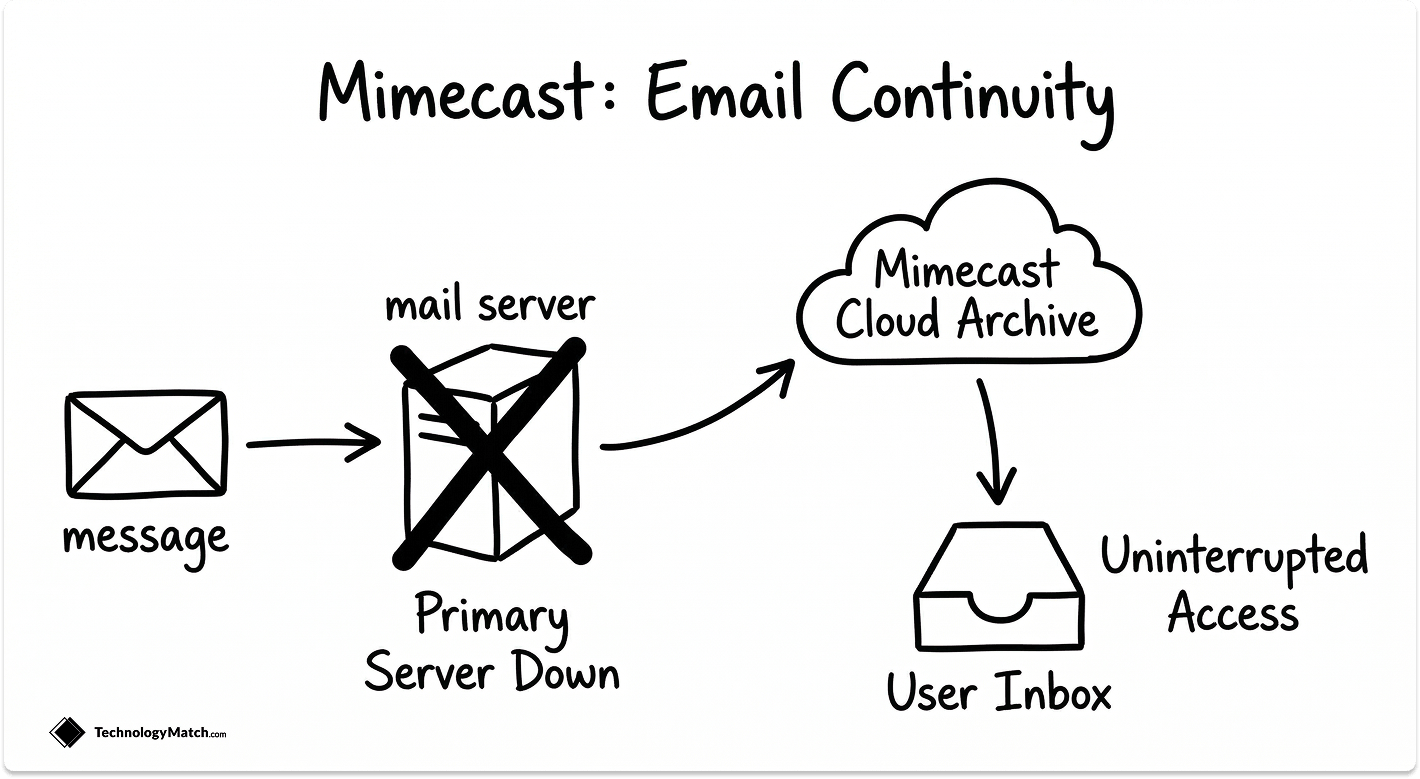
Mimecast maintains a cloud archive of your email that acts as a continuity layer if your primary email environment goes down. For organisations where email availability is a business-critical requirement, that is a meaningful differentiator.
Where Mimecast is Strongest
Email continuity. Mimecast's continuity service gives users access to recent emails and the ability to send and receive during an outage. Whether that is a Microsoft 365 incident, a ransomware attack on your mail server, or an ISP failure. This is a capability Proofpoint and Abnormal do not offer in the same integrated way.
Administration and total cost of ownership. Mimecast consistently scores higher than Proofpoint on ease of administration in third-party reviews. The policy management interface is cleaner, reporting is more accessible to generalist IT administrators, and onboarding is faster.
For a lean IT team without dedicated email security headcount, this operational difference matters. It is the same calculus that drives many mid-market organisations toward co-managed IT models over fully in-house security operations.
Impersonation protection. Mimecast's Impersonation Protect layer specifically targets executive impersonation and domain lookalike attacks. A strong capability for organisations that are concerned about spear-phishing targeting their leadership team.
URL and attachment protection. Mimecast's URL protection and attachment sandboxing cover the majority of commodity and moderately sophisticated threats. For most organisations, the detection rate difference between Mimecast and Proofpoint on known threat types is not operationally significant.
Where Mimecast Falls Short
Mimecast's BEC detection for text-only, socially engineered attacks is weaker than both Proofpoint and Abnormal. Attacks containing no malicious URL, no attachment, and no known threat signature are where Mimecast users report the most misses.
This is not a configuration problem. It is an architectural one. A gateway-based model that inspects content cannot catch an attack that has no malicious content to inspect.
Pricing: Generally more cost-effective than Proofpoint at comparable feature tiers. Mid-market pricing typically runs $20 to $40 per user per year depending on modules.
Best for: Mid-market organisations between 200 and 2,000 employees that need strong gateway protection, email continuity, and manageable administration without the complexity or cost of an enterprise platform.
Abnormal Security: The AI-Native Challenger Built for What SEGs Miss
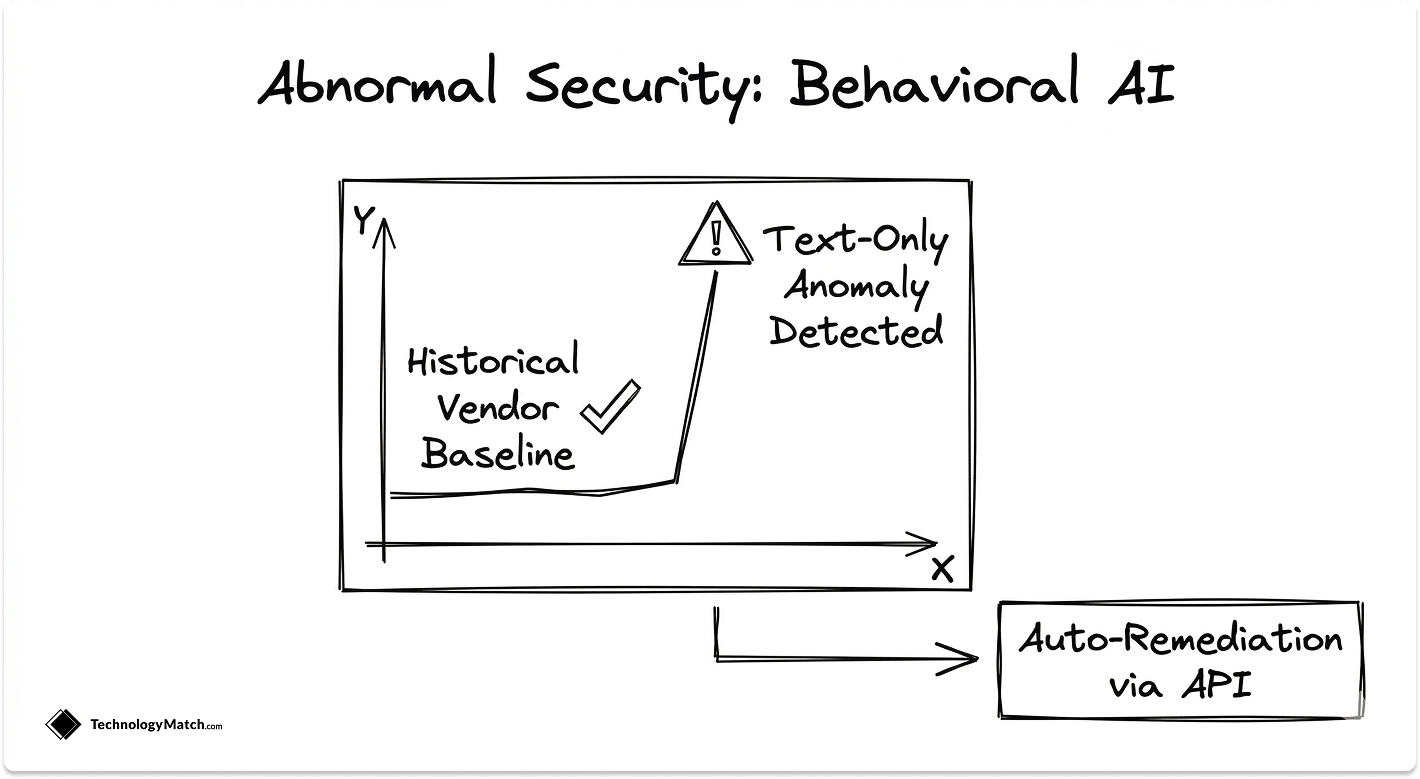
Abnormal Security was founded in 2018 on a specific thesis. The attacks that cause the most financial damage are architecturally impossible for traditional email gateways to catch.
A plain-text email from a spoofed domain asking a finance manager to wire funds has no URL to scan, no attachment to sandbox, and no known malware signature. The only way to catch it is to understand whether the message is consistent with how that sender normally communicates with that recipient.
That is exactly what Abnormal does. It ingests your historical email data, builds behavioural profiles for every user, every internal sender, and every vendor relationship, and flags messages that deviate from established patterns, even when they contain no technically malicious content.
Where Abnormal is Strongest
BEC and vendor email compromise (VEC). This is Abnormal's core capability and where it has the clearest architectural advantage over SEGs. Gartner Peer Insights users rate Abnormal at 4.8 out of 5, the highest rating in the email security category.
VEC is the attack vector most organisations are least prepared for. When an attacker compromises a legitimate vendor's email account and uses it to redirect a payment, there is no spoofed domain to flag and no reputation signal to trigger. The only defence is a platform that knows what normal looks like for that vendor relationship. This is closely related to the vendor risk exposure covered in our vendor risk assessment guide.
Deployment speed. Abnormal connects via Microsoft 365 or Google Workspace API with no MX record changes. Most organisations are fully deployed and seeing detections within 24 to 48 hours. For comparison, a SEG deployment typically takes two to four weeks including MX record propagation, policy configuration, and staged rollout.
SOC time reduction. Abnormal automates the remediation of detected threats. It pulls flagged messages from user inboxes automatically and generates structured remediation reports. The company reports a 95% reduction in SOC time spent on email security, which aligns with what practitioners report publicly.
For lean security teams, this matters directly in terms of budget. Hours your analysts spend triaging email security alerts are hours they are not spending on the MDR and XDR detection work that requires human judgment.
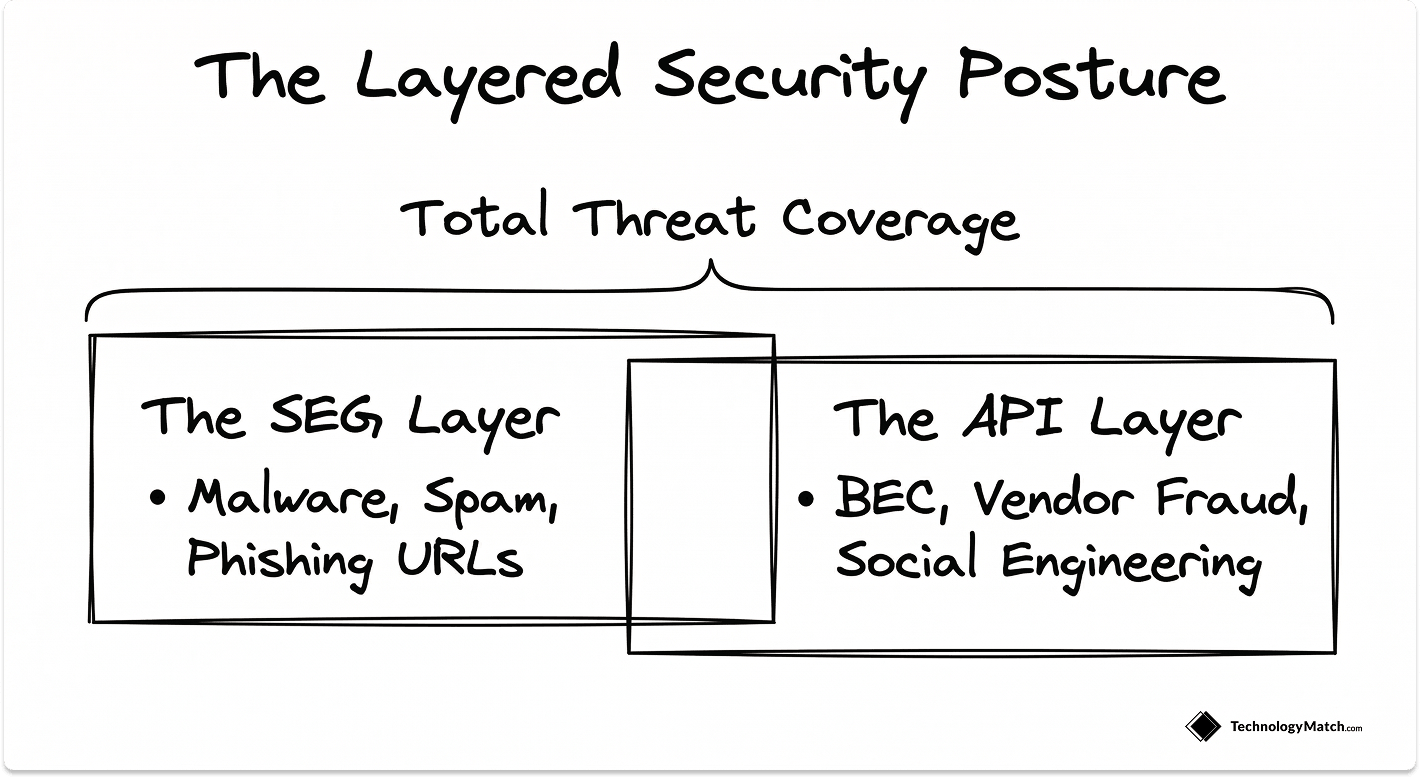
Layering with existing SEGs. Abnormal is designed to run alongside Microsoft Defender for Office 365, Proofpoint, or Mimecast, not replace them. Many organisations run Abnormal as a second layer specifically for BEC and VEC coverage.
Where Abnormal Falls Short
Abnormal does not replace a SEG for known threat coverage. It will not scan attachments in a sandbox, rewrite URLs, or block spam at the gateway level. Organisations that deploy Abnormal without a separate SEG are relying entirely on their email provider's native filtering for commodity threats.
The platform also requires Microsoft 365 or Google Workspace. It does not support on-premises Exchange environments, which remains a disqualifier for some regulated industries and government entities.
Pricing: Typically $50 to $80 per user per year depending on modules. Not publicly listed.
Best for: Organisations running Microsoft 365 or Google Workspace that are primarily concerned with BEC, VEC, and socially engineered attacks. Most effective when layered on top of an existing SEG.
Head-to-Head Comparison
The Decision Framework
The wrong way to approach this decision is to start with vendor demos. Start with your threat data.
Pull your last 12 months of email security incidents. What categories dominate? Spam, malicious attachments, phishing URLs, or socially engineered text-only fraud? If the answer is the first three, a SEG is the right primary investment. If the answer is the last one, Abnormal's architectural model addresses the problem directly.
Assess your team's operational capacity. Proofpoint's depth of capability comes with administrative overhead. If you don't have a dedicated email security analyst or a SOC, Mimecast's lower administrative burden or Abnormal's automated remediation will deliver better real-world outcomes in practice.
Evaluate your compliance requirements. If you need integrated email archiving, DLP, and threat protection from one vendor, Proofpoint's unified platform reduces integration complexity. Mimecast also offers archiving. Abnormal does not. If you are running a formal IT vendor due diligence process before shortlisting, factor data handling, residency, and SOC 2 certification into your evaluation criteria alongside detection capabilities.
Consider layering, not replacing. The strongest email security postures run a SEG for known-threat coverage and Abnormal for BEC and VEC detection. If budget allows, Mimecast plus Abnormal or Proofpoint plus Abnormal addresses the full threat spectrum more completely than any single platform.
This is the same principle that drives the best IT vendor selection processes. The question is never which single vendor wins. It is which combination of vendors closes your actual risk gaps.
Red Flags to Watch in Vendor Evaluations
Vendors that benchmark against spam catch rates. Any of the three platforms will catch 99% or more of spam. That metric is meaningless for procurement decisions. Ask for BEC detection rates and false positive rates on legitimate business email specifically.
SEG vendors that claim to solve BEC without explaining how. URL rewriting and attachment sandboxing do not address text-only fraud. If a vendor cannot explain the specific mechanism by which they detect a plain-text impersonation email, they are not solving the problem.
Abnormal demos that only show obvious BEC examples. Ask to see how the platform handles a vendor relationship where communication frequency recently changed. That is the real edge case that reveals whether the behavioural baseline is genuinely granular or a demo environment tuned for presentations.
Contracts without defined false positive SLAs. Email security false positives have direct business impact. Legitimate vendor invoices quarantined, executive communications blocked, finance approvals delayed. Any contract that does not include a false positive rate commitment and a remediation process gives the vendor no accountability for operational disruption. Review our SLA management guide for the specific clauses to negotiate before you sign.
The Right Email Security Platform Starts With Your Threat Profile
Proofpoint wins on payload coverage and compliance depth. Mimecast wins on operational simplicity and continuity. Abnormal Security wins on BEC and vendor fraud detection that gateways cannot catch.
No single platform closes every gap. The strongest postures layer a SEG for known threats and Abnormal for socially engineered fraud.
Start with your threat data, not vendor demos. Pull your last 12 months of incidents, match the architecture to the attack type, and use the selector tool above to get a starting point.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
Can I run Abnormal Security alongside Proofpoint or Mimecast?
Yes, and this is the deployment model Abnormal recommends. It operates independently of your mail flow via API and will not conflict with your existing SEG. Most organisations that deploy Abnormal are adding it on top of an existing gateway, not replacing it.
Does Mimecast work with Microsoft 365?
Yes. Mimecast integrates with Microsoft 365 via connectors and API, replacing Microsoft's native filtering in your mail flow and adding its own protection layer on top.
What is vendor email compromise (VEC) and why does it matter?
VEC is a specific variant of BEC where an attacker compromises a legitimate vendor's email account and uses it to send fraudulent invoices or payment redirect requests. Because the email comes from a real account at a real domain, reputation-based filters cannot catch it. Abnormal's behavioural baseline approach tracks expected communication patterns between your organisation and that vendor, which is the most effective current defence against this attack type.
Is Microsoft Defender for Office 365 a viable alternative?
For organisations with tight budgets and a low threat profile, Defender for Office 365 Plan 2 covers commodity threats adequately. It is not competitive with Proofpoint or Abnormal for BEC detection or targeted attack protection. Organisations in financial services, professional services, healthcare, or legal should layer a dedicated platform on top of native Microsoft protection.
How long does an Abnormal Security deployment take?
Most deployments are operationally live within 24 to 48 hours. The platform requires approximately 14 days of historical data ingestion to build a fully calibrated behavioural baseline. During that period, detections are flagged but remediation thresholds are more conservative while the baseline stabilises.