The Best IT Outsourcing Companies for IT Leaders: How to Evaluate and Select the Right Partner
A practical guide to evaluating and selecting IT outsourcing companies: the three delivery models, a curated vendor shortlist, five selection criteria, and the contract terms you cannot skip.

Every IT outsourcing engagement starts the same way: a vendor promises to reduce costs, improve service quality, and free your team to focus on strategic work. A year later, you're managing the vendor relationship as a second job, internal users are complaining louder than before, and the contract you signed has carve-outs that make accountability impossible.
The failure point is almost never the vendor. It's the selection process. According to Deloitte's 2024 Global Outsourcing Survey, 70% of executives report their vendor management function is not fully mature, meaning most organisations are outsourcing significant IT functions to external providers without the governance structure to manage them effectively.
This guide covers how to choose the right outsourcing model before you look at a single vendor, what to look for in a provider, a curated list of companies worth evaluating, and the contract terms you cannot afford to skip.
The Three IT Outsourcing Models — And Which One You Actually Need
The most expensive mistake in IT outsourcing is selecting a delivery model that doesn't match your operational reality. These three models are frequently conflated in vendor proposals, and vendors will rarely volunteer which one fits you best.
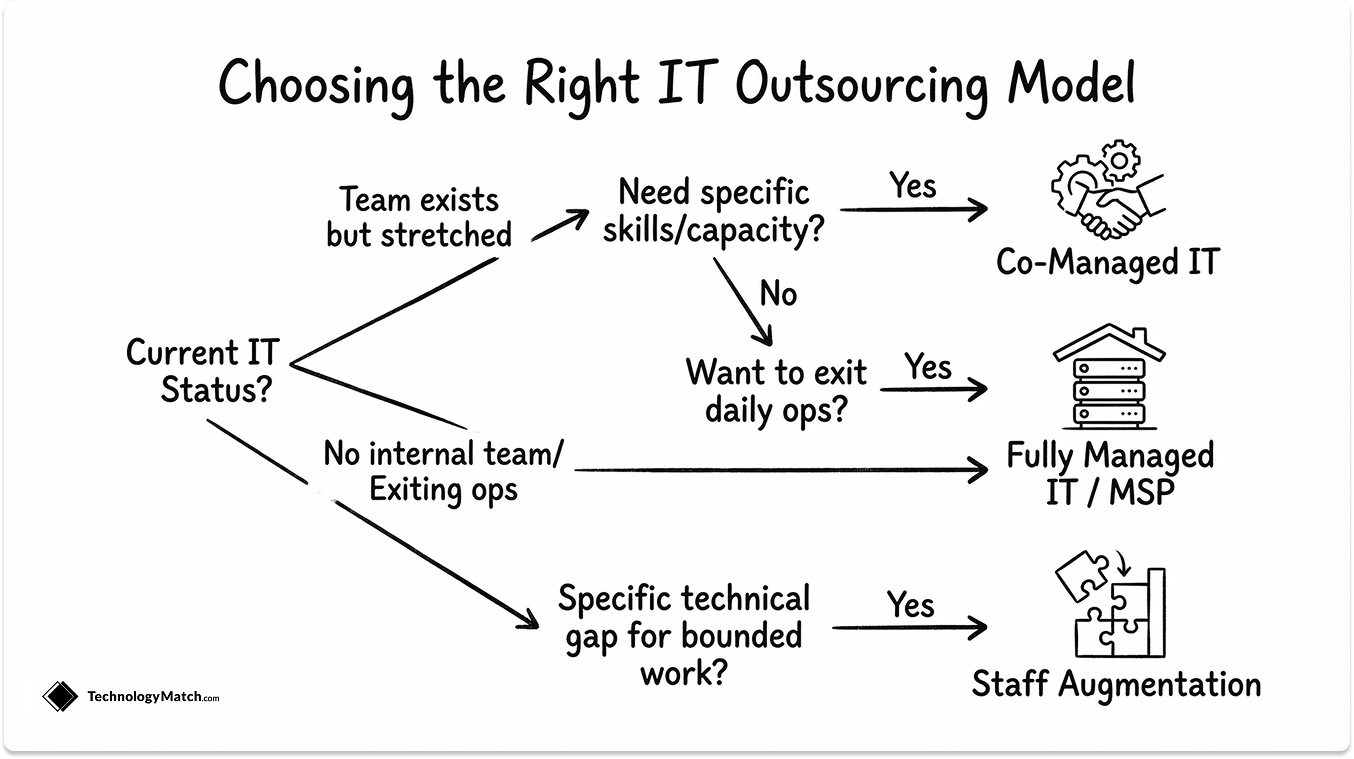
Co-Managed IT
Your internal team stays in place. The provider fills gaps: helpdesk overflow, after-hours coverage, specialised skills for cloud, security, or compliance work. The internal IT lead retains ownership of the roadmap and vendor relationships. The provider is an extension of your team, not a replacement.
This model works best when you have an IT function that is functional but stretched. You're not trying to exit IT operations. You need capacity and specific expertise without the overhead of additional headcount.
Fully Managed IT (MSP Model)
The provider owns IT operations end-to-end: helpdesk, infrastructure monitoring, patch management, backup, and security operations. Your team's involvement is governance and escalation, not daily IT management.
This is the right model for SMBs without a mature internal IT function, or for larger organisations deliberately exiting day-to-day IT operations to focus internal resources on application development, data, or digital transformation. It is not the right model if you still want meaningful control over day-to-day IT decisions.
For a deeper look at what to look for before signing an MSP agreement, the IT Buyer's Guide to Managed IT Services covers the full evaluation process. And if you want to read more about how MSPs differe from MSSPs and Co-managed IT, this guide covers it in detail.
Staff Augmentation
Individual contractors or small specialist teams embedded in your organisation for defined projects. Cloud migration, ERP rollout, security architecture review, network redesign. The engagement has a defined scope and end date. Governance stays entirely with your team.
Use staff augmentation when you have a specific technical gap for a bounded piece of work. Do not use it as a long-term substitute for full-time IT staffing — the cost differential at scale is significant, and knowledge retention walks out with the contractor.
A quick decision filter:
Your SituationRight ModelInternal IT team exists but is under-resourcedCo-Managed ITNo internal IT team, or actively exiting IT opsFully Managed ITSpecific project requiring specialist skillsStaff AugmentationMix of ongoing ops + project workCo-Managed IT + targeted augmentation
Which Model is Right for You
What to Outsource and What to Keep In-House
Not everything in your IT portfolio belongs in a vendor's hands. The distinction matters because scope creep in outsourcing contracts is one of the leading causes of cost overruns. Define the boundaries before the conversation starts.
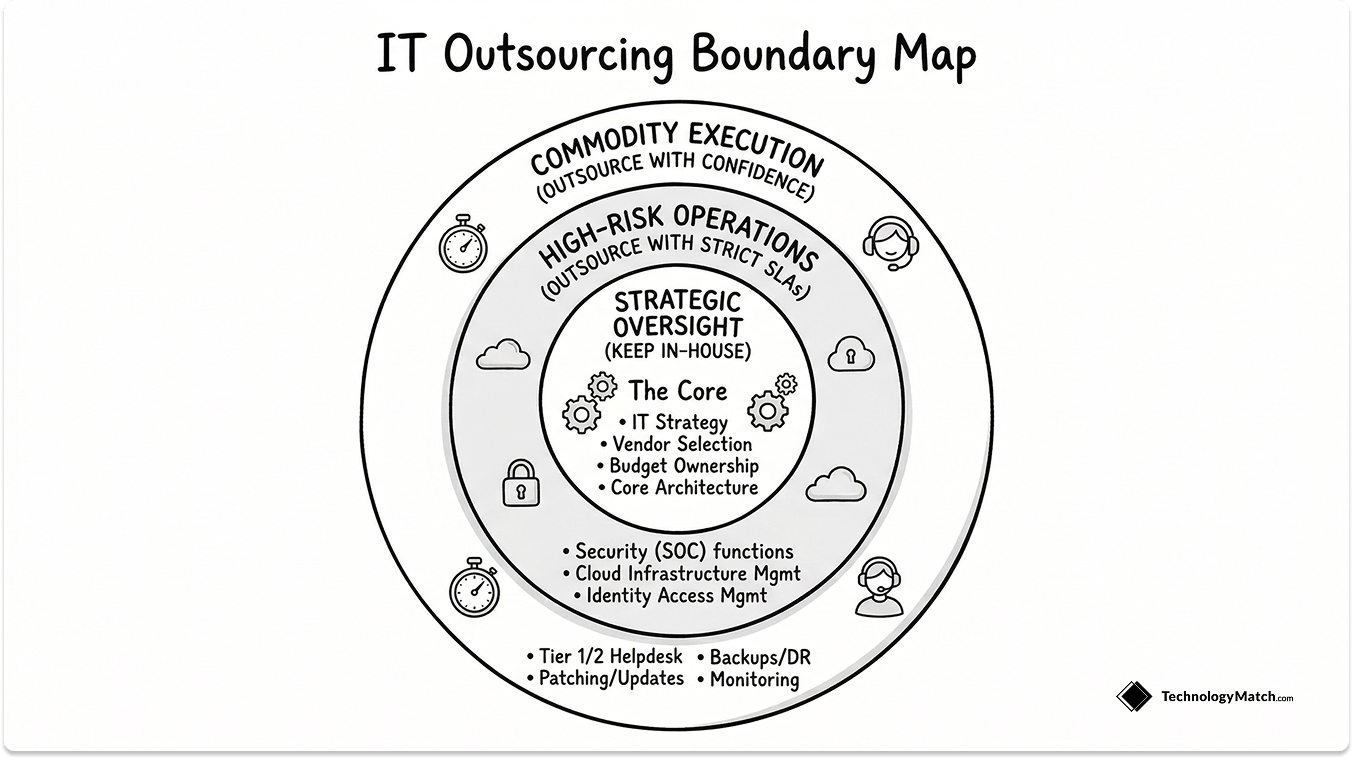
Outsource with confidence:
- Tier 1 and Tier 2 helpdesk support
- Network monitoring and alerting
- Patch management and software updates
- Backup and disaster recovery operations
- Hardware procurement and asset tracking
- After-hours infrastructure monitoring
Outsource with explicit SLA controls:
- Security operations (SOC functions, threat monitoring, incident response)
- Cloud infrastructure management (provisioning, cost governance, access controls)
- Identity and access management operations
Keep in-house or retain direct strategic oversight:
- IT strategy and technology roadmap
- Vendor selection decisions — including this one
- Data governance policy and data classification
- Budget ownership and contract approval authority
- Architecture decisions for core business systems
The principle is straightforward: outsource execution, retain ownership of decisions that shape your organisation's technical direction. When a provider starts influencing your technology choices in ways that conveniently increase their scope or lock you into their tool stack, that is a governance failure, not a vendor feature.
The Best IT Outsourcing Companies for IT Leaders
These companies are segmented by the model they're best suited for. This is not an exhaustive market map — it is a shortlist of providers worth serious evaluation based on their track record, service depth, and relevance to mid-market and enterprise IT teams.
For Co-Managed IT
Best fit for organisations in the 100–1,000 employee range that retain an internal IT team but need helpdesk augmentation, security operations support, or cloud expertise. Ntiva's co-managed model gives your internal lead visibility into all tickets and escalations. Watch-out: geographic coverage is stronger in the Northeast and Mid-Atlantic US; confirm coverage if your organisation is distributed.
Strong for mid-market companies that need co-managed IT with a security-forward posture. Logically bundles SOC capabilities into its co-managed offering, which matters if your team lacks internal security operations depth. Watch-out: their pricing model is user-based; confirm exactly what's included per user before you compare quotes.
Thrive positions itself at the intersection of managed IT and cybersecurity, making it a solid fit for regulated industries (financial services, legal, healthcare) that need co-managed support with compliance-aware operations. Watch-out: service quality can vary by regional office; get references from clients in your specific geography.
For Fully Managed IT — SMB to Mid-Market
A strong option for organisations in the 50–500 employee range looking for a single provider to own IT operations, helpdesk, and security monitoring. Dataprise has significant depth in hybrid environments (on-premises + cloud). Watch-out: response times for P2 and P3 incidents can vary; push for tiered SLA commitments with specific resolution targets in writing.
Primarily serves mid-market organisations running SAP environments, making them a specialised fit if your business is SAP-dependent and needs a managed IT partner with deep ERP integration experience. Watch-out: if you're not on SAP, their differentiation is less compelling compared to generalist MSPs.
For Fully Managed IT — Enterprise
Spun out of IBM's managed infrastructure division, Kyndryl operates at genuine enterprise scale — mainframe, hybrid cloud, and complex multi-vendor environments. Best fit for large organisations with legacy infrastructure that generalist MSPs cannot support. Watch-out: engagement models can be slow-moving for organisations that need operational agility; contract flexibility is limited.
HCLTech covers the full spectrum of IT outsourcing from infrastructure management to application services, with strong delivery capability in Europe, North America, and APAC. Their engineering depth makes them a credible choice for enterprises with complex multi-cloud or digital transformation programmes running in parallel with outsourced IT ops. Watch-out: account management quality varies significantly; establish named escalation contacts at senior level before signing.
A broad IT services and outsourcing provider with deep capability in cloud, cybersecurity, and network managed services. Wipro's scale works in your favour for global coverage requirements. Watch-out: like most large providers, delivery is only as good as the account team assigned to you. Negotiate team continuity clauses into the contract.
For Staff Augmentation and Project-Based Work
One of the largest IT staffing and services firms in North America. Strong bench for infrastructure, security, cloud, and enterprise application roles. Reliable for both short-term placements and longer project engagements. Watch-out: rates vary significantly by market; benchmark against two or three competing firms before accepting the first proposal.
Broad IT staffing coverage with strong penetration in enterprise accounts. Good option for building out temporary project teams where cultural fit and communication skills matter as much as technical capability. Watch-out: vetting depth varies by recruiter; specify technical screening requirements explicitly rather than relying on generic job descriptions.
For organisations that need project-based engagement with a provider capable of delivering at scale — cloud migrations, digital transformation programmes, large-scale infrastructure refreshes. Cognizant's delivery model is well-suited to defined-scope, outcome-based engagements. Watch-out: project governance requires active client ownership; do not expect the provider to drive programme management without a strong internal counterpart.
5 Selection Criteria That Separate Good Providers From Expensive Problems
A vendor's sales team will present case studies, reference logos, and an SLA document. None of that tells you whether the provider will perform once the contract is signed. These five criteria do.
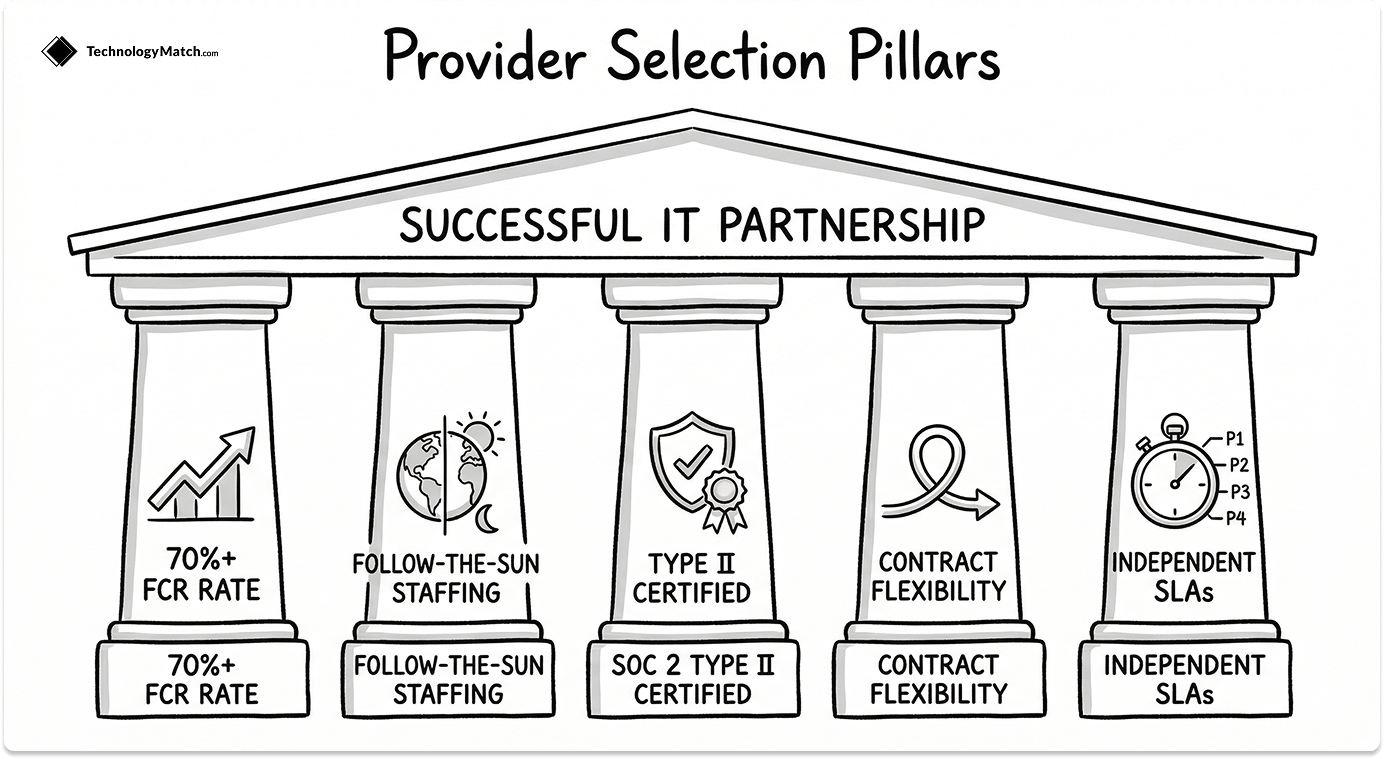
1. First Contact Resolution Rate
The single most revealing operational metric for any outsourced helpdesk engagement is the first contact resolution (FCR) rate — the percentage of tickets resolved at Tier 1 without escalation. Industry benchmarks from MetricNet put best-in-class at 70% or above.
Ask every provider you evaluate for their current FCR rate across their existing client base, not just their best-performing account. A provider sitting at 55% FCR means 45% of your users' issues are being escalated — and your team, or a higher-cost Tier 2 resource, is picking them up. That is not cost reduction. That is cost displacement.
2. Geographic Coverage and Staffing Model
24/7 coverage is a standard claim. What you need to verify is the staffing model behind it. Does the provider run genuine follow-the-sun operations with engineers in multiple regions, or do they run a single overnight team handling all after-hours volume at reduced capacity?
For any global IT outsourcing requirement, confirm: which geographies have dedicated staffing, what languages are supported at Tier 1, and what the escalation path looks like outside business hours in your primary operating regions.
3. Security Certifications — The Minimum Bar
SOC 2 Type II is the baseline. It is not a differentiator; it is a qualification threshold. A provider without a current SOC 2 Type II report is not in consideration for any IT outsourcing engagement that involves access to your infrastructure, user data, or systems.
For regulated industries, the requirements go further:
- Healthcare: HIPAA Business Associate Agreement (BAA) capability, with documented data handling practices
- Financial services: SOC 1 Type II, plus alignment with relevant frameworks (PCI-DSS if cardholder data is in scope)
- Government or public sector: FedRAMP authorisation for cloud-hosted components
Ask for the actual certification documentation, not a statement that the certification exists. Certifications expire. Request the most recent audit report date.
4. Contract Flexibility and Exit Terms
A three-year lock-in with no performance-based exit clause is a liability, not a partnership. Before signing, confirm three things:
First, what triggers a termination-for-cause right and what is the notice period? Second, who owns the configurations, documentation, IP, and data the provider has created or touched during the engagement — make sure the answer is you, and that it is written into the contract. Third, what does the offboarding process look like, and is there a documented transition period?
Providers confident in their service quality will negotiate reasonable exit terms. Those who resist are telling you something about what they expect the relationship to look like.
5. SLA Structure and Measurement
An SLA is only as credible as the method used to measure it. The provider should be reporting against independently verifiable data, not a dashboard they control. Push for P1 through P4 response and resolution commitments segmented by priority tier, breach remedy clauses with real financial consequence, and monthly reporting in a format you specify.
For a detailed framework on how to structure and enforce vendor SLAs — including the contract clauses designed to protect the vendor rather than you — the SLA Management for IT Leaders guide covers exactly what to negotiate before you sign.
Red Flags in an IT Outsourcing Proposal
Some warning signs only become visible when you are deep into evaluation. These are worth checking before you get there.

No named team assigned to your account. A provider who cannot tell you which engineers and account leads will be responsible for your environment at the proposal stage is telling you that your account will be managed as interchangeable resource time. That is acceptable for commodity helpdesk. It is not acceptable for anything involving your infrastructure or security operations.
SLA response times measured from ticket creation, not incident start. A critical system can be down for 45 minutes before a user opens a ticket. If the provider's P1 clock starts at ticket creation, your actual time to resolution is 45 minutes longer than the SLA implies. Require that SLA measurement starts at the confirmed incident time, not the ticket timestamp.
Per-user pricing with no definition of scope. Per user per month is meaningless without a clear definition of what is included. Confirm whether patch management, endpoint monitoring, backup, and security tools are included in the per-user rate or billed separately. Scope ambiguity in outsourcing contracts is almost always resolved in the vendor's favour.
No documented offboarding process. A provider that has not thought about how you exit the relationship has not thought seriously about what happens when things go wrong. Offboarding procedures should be documented in the contract before you sign, not negotiated under duress when you decide to leave.
References drawn entirely from one industry or company size. If every reference is a 50-person professional services firm and you run a 3,000-person manufacturing organisation, those references tell you almost nothing about how the provider will perform for you. Ask specifically for references that match your industry, scale, and infrastructure complexity.
How to Structure the IT Outsourcing Contract
Three provisions are non-negotiable. Everything else is negotiable.

Scope of work with exclusions listed explicitly. Vague scope is the single largest source of billing disputes and relationship breakdowns in IT outsourcing. The contract should define not only what the provider is responsible for, but what is explicitly out of scope. If it is not listed as in-scope, assume it is excluded and will be charged as additional work.
Data ownership and portability. Every configuration the provider builds in your environment, every piece of documentation they produce, and every data set they touch belongs to you. This needs to be stated explicitly in the contract, with a defined process for transferring that material on exit. Providers sometimes treat proprietary tooling or documentation as their IP by default. Challenge that position before you sign, not after.
Termination for cause rights with defined breach thresholds. A termination clause that requires material breach without defining what constitutes material breach is unenforceable in practice. Define the specific SLA failures, breach frequency, or performance thresholds that trigger a termination right. Combine this with a 30-day cure period and a clean exit process. This provision protects both parties — a credible provider will not object to it.
For the full due diligence process that should precede any IT outsourcing contract, including security verification and financial stability checks, the IT Vendor Due Diligence guide covers what to verify before the first proposal review. And for the governance structure that should sit on top of any outsourcing relationship once it's live, the IT Vendor Compliance Framework covers how to structure oversight across your full vendor portfolio.
Matching the Right Provider to Your Requirements
A survey found that 80% of executives plan to maintain or increase investment in third-party outsourcing. The market is growing because IT complexity is growing — more vendors, more cloud environments, more security surface area, and more pressure on lean internal teams to manage all of it.
The IT outsourcing companies that deliver value over a three-to-five year relationship share a few consistent characteristics: they assign dedicated, named teams to accounts rather than treating clients as pooled resource demand, they operate on independently verifiable SLA data rather than self-reported metrics, and their contracts are written to reflect a genuine service relationship rather than a liability management exercise.
The IT Vendor Selection guide covers the broader evaluation process, including how to run an RFP that surfaces these characteristics before you reach the contract stage. The right outsourcing partner reduces the cognitive load of running IT infrastructure — not just the headcount cost. That distinction determines whether the engagement delivers what was promised, or becomes a vendor management problem you are paid to solve.
Looking for IT partners?
Find your next IT partner on a curated marketplace of vetted vendors and save weeks of research. Your info stays anonymous until you choose to talk to them so you can avoid cold outreach. Always free to you.
FAQ
What is the difference between co-managed IT and a fully managed MSP?
Co-managed IT extends your existing internal team — your IT staff stays in place, and the provider fills capacity gaps, handles helpdesk overflow, or brings specialist skills in areas like cloud or security. A fully managed MSP replaces your internal IT function entirely. One provider owns the full stack: helpdesk, patching, monitoring, backup, and security. The right choice depends on whether you have an internal team worth keeping and how much control you want to retain over day-to-day IT decisions.
How do I know if my organisation is ready to outsource IT?
Three signals indicate readiness: your internal team is spending more time on reactive support than strategic work, you have recurring incidents that expose skill gaps you can't hire for fast enough, and IT costs are unpredictable quarter to quarter. Outsourcing is not a fix for a broken IT function — it amplifies whatever governance structure you already have. Before you engage a provider, document your current environment, define what success looks like, and establish the internal owner who will manage the vendor relationship.
What should I never outsource to an IT provider?
IT strategy, data governance, and vendor selection decisions should stay in-house. The moment you outsource the decision of which tools and platforms your organisation runs on, you hand a provider the ability to create lock-in by design. Execution — helpdesk, patching, monitoring, infrastructure management — is safe to outsource. The judgment calls that shape your technology roadmap are not.
How do I evaluate an IT outsourcing provider before signing a contract?
Ask for their First Contact Resolution (FCR) rate — the industry benchmark is 70% or above. Request references from clients in your industry and at your company size, not just their best-case logos. Review the contract for three non-negotiables: scope exclusions (what they will not cover), data portability terms (what happens to your data if you leave), and defined breach thresholds that trigger your right to exit without penalty. If a provider resists sharing FCR data or won't negotiate exit terms, that tells you everything you need to know about how they operate under pressure.
What is a realistic timeline for onboarding a managed IT provider?
For a co-managed engagement, expect four to six weeks from contract signature to fully operational — longer if your environment is undocumented. For a fully managed MSP taking over an existing IT function, budget eight to twelve weeks minimum. The onboarding phase is where most engagements fail: providers underestimate the complexity of inheriting an environment, and clients underestimate the internal effort required to hand it over cleanly. Insist on a formal onboarding plan with defined milestones and a named transition owner on both sides before you sign.