Cisco vs Fortinet vs Palo Alto vs HPE Aruba Edgeconnect: An SD-WAN Comparison Guide for 2026
Compare SD-WAN solutions: Cisco, Fortinet, Palo Alto, and HPE Aruba Edgeconnect SD-WAN. Architecture, SASE readiness, pricing, and an interactive tool to match each platform to your needs.

The SD-WAN market hit $7.9 billion in 2025 and is tracking toward $21.7 billion by 2030, growing at 22.3% annually.
The decision is no longer whether to deploy SD-WAN. It is which platform you build on for the next five years, and what that choice locks you into architecturally.
Four vendors dominate enterprise procurement in the US right now: Cisco, Fortinet, Palo Alto Networks, and HPE Aruba. They share market prominence, but they take genuinely different approaches to architecture, security, and operational management. Each carries a different set of trade-offs.
This comparison evaluates all four on the same criteria, with the same level of scrutiny.
How to Read This Comparison
Every vendor below is evaluated on six dimensions:
- Architecture and deployment model
- Security integration and SASE readiness
- AI and automation capabilities
- TCO and licensing
- Operational overhead and management
FYI, SD-WAN contracts are easy to sign and hard to exit. Get the shortlist right first. Tell us your environment, team size, and SASE requirements and we'll match you with vendors that fit.
We can also prep the vendors so your conversation begins with context. Plus a $50 gift card for completing a demo. Start with the survey below so we can get to know you better. And it's free.
Cisco Catalyst SD-WAN
Architecture
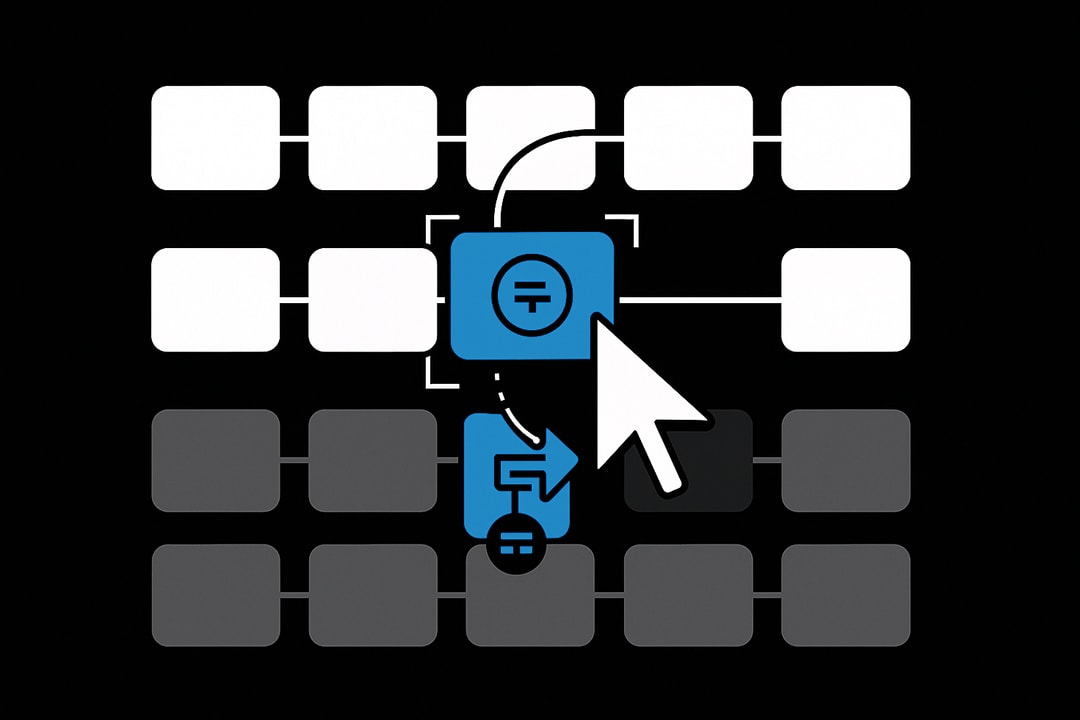
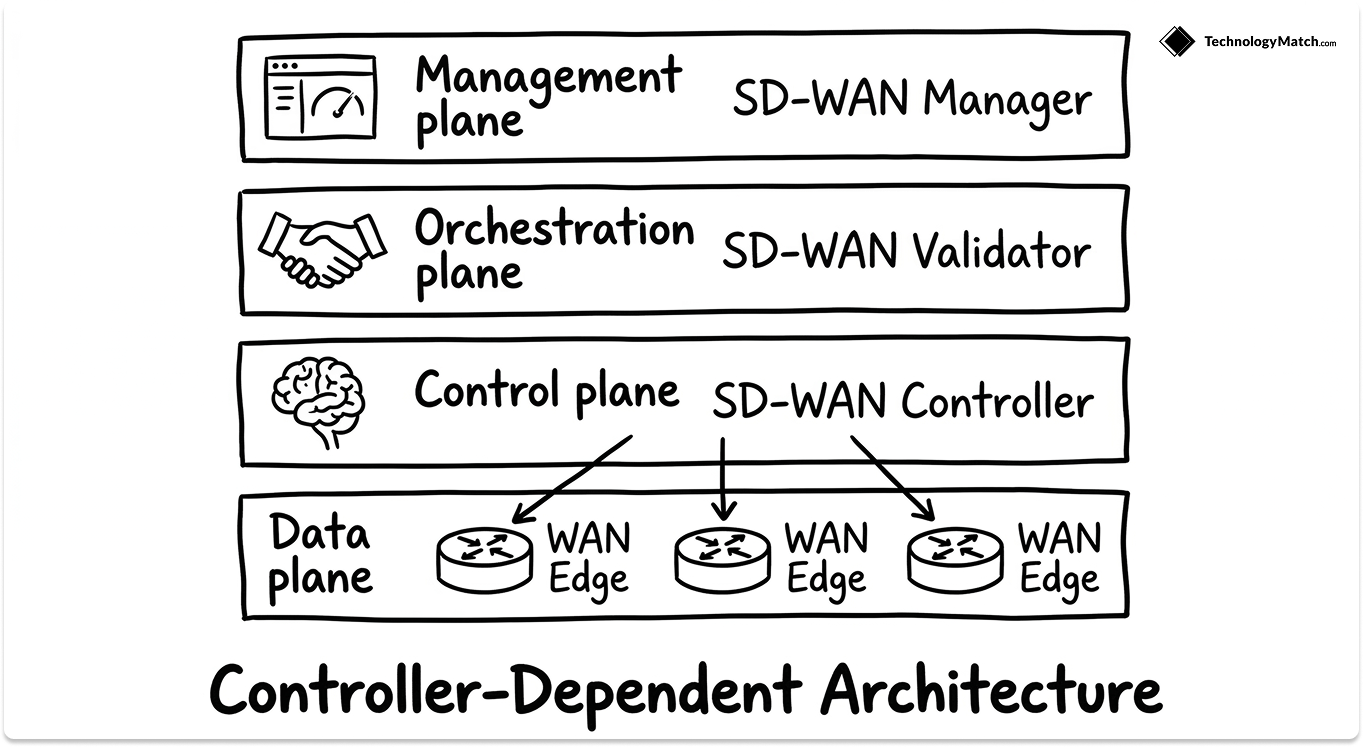
Cisco Catalyst SD-WAN, built on the Viptela stack, runs a four-plane architecture: management (SD-WAN Manager), control (SD-WAN Controller), orchestration (SD-WAN Validator), and data plane (WAN Edge routers).
The control plane distributes routing and policy via the Overlay Management Protocol (OMP). Data plane encryption runs AES-256 GCM.
This is a controller-dependent architecture. Path selection and policy propagation originate from a central controller and flow down to edge devices. It runs on Catalyst 8000 series routers and supports on-premises, cloud-hosted, and FedRAMP High-Ready (AWS and Azure GovCloud) deployments.
Cisco also sells Meraki SD-WAN as a separate product aimed at smaller environments. Both products share a parent company, but operate on separate management planes.
Where Cisco Is Strong
Enterprise track record and scale are unmatched. Cisco Catalyst SD-WAN has over 48,000 deployments globally and is embedded in 70% of Fortune 100 companies. At this scale, integration playbooks, professional services, and partner ecosystems are mature in ways no competitor can match.
Routing depth is a real differentiator. Catalyst SD-WAN supports Segment Routing over IPv6 (SRv6), enabling deterministic traffic engineering across multi-carrier topologies. For organizations managing complex, multi-MPLS-provider WANs, the routing capability on this platform is not matched by Fortinet, Palo Alto, or Aruba.
The ecosystem runs deep. ThousandEyes provides first, middle, and last-mile visibility. Umbrella handles cloud DNS security. Catalyst Center manages campus and branch policy from a unified plane. If you are already running a primarily Cisco infrastructure, the integration surface area is extensive.
Certifications are the broadest in this group. FIPS-140-2, Common Criteria, PCI DSS, FedRAMP High-Ready, and MEF SD-WAN 3.0 are all supported.
Where Cisco Falls Short
Licensing is the most consistent complaint from enterprise buyers. Cisco's subscription model involves tiered structures, bandwidth-dependent pricing, and 1/3/5-year term commitments. The total cost is difficult to forecast, particularly as organizations scale. It is not a cheap product by any means.
SASE management is split. Cisco's SASE strategy requires integrating Catalyst SD-WAN Manager with Cisco Secure Access for SSE. That means two separate management consoles; absence of a unified management place. If converged SASE management is on your roadmap, this is a structural issue, not a roadmap item.
Security visibility lags competitors. Cisco's application identification relies on static IP whitelisting for many SaaS platforms rather than dynamic application recognition. So, the visibility part in other solutions is better compared to Cisco.
Vendor lock-in is a documented operational concern. Cisco should consider focusing on SD-WAN compatibility with other environments and not being so vendor-locked with Cisco.
CISA issued an emergency directive in February 2026. Cisco Catalyst SD-WAN Controller was found to contain an actively exploited critical vulnerability allowing attackers root access. Threat actors had been exploiting it since 2023. This required urgent coordinated patching across all control plane components.
Who It's Built For
Cisco Catalyst SD-WAN suits large enterprises already deeply invested in the Cisco ecosystem, with dedicated network engineering teams and complex multi-carrier WAN topologies where SRv6 routing depth matters.
It is a poor fit for lean IT teams, organizations seeking a clear SASE path, or any buyer prioritizing cost efficiency over ecosystem integration.
Also read: Cisco vs. Aruba vs. Arista: Which Network Infrastructure Vendor Should IT Leaders Choose?
Fortinet Secure SD-WAN
Architecture
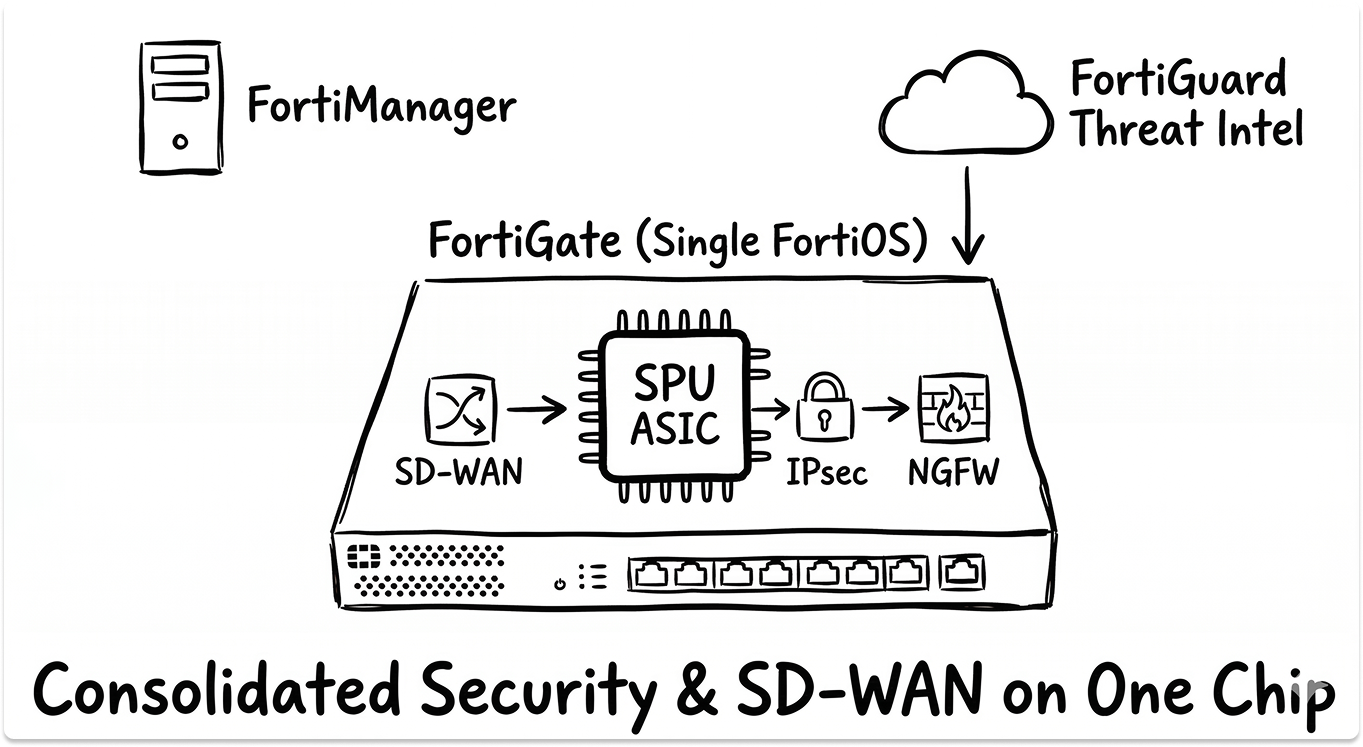
Fortinet's architecture is structurally distinct from every other vendor here. The NGFW and SD-WAN engine run on the same FortiGate appliance under a single operating system, FortiOS. Every FortiGate is simultaneously an SD-WAN edge router, IPsec VPN concentrator, and full-stack security gateway. There is no separate security appliance at the branch.
Path selection, security inspection, and policy enforcement happen on the same device at hardware speed, powered by Fortinet's custom Security Processing Unit (SPU) ASICs. These deliver SSL and IPsec inspection up to 100 Gbps on high-end models.
Fortinet uses a controllerless data plane. Each FortiGate evaluates WAN path quality and makes routing decisions independently, without depending on a central controller.
FortiManager handles centralized policy management, but branches maintain local routing autonomy. In failure scenarios, sites keep routing even when the management plane is unreachable.
Where Fortinet Is Strong
The analyst record is the strongest on this list. In the 2025 Gartner Peer Insights Voice of the Customer report, Fortinet received 414 reviews, the highest of any SD-WAN vendor, with a 4.9/5 rating and 97% recommendation rate.
Security efficacy is independently validated. CyberRatings awarded Fortinet AAA for security efficacy. FortiGuard Labs threat intelligence integrates directly into path selection policies, meaning security posture actively influences routing decisions, not just traffic inspection after the fact.
Application visibility is operationally superior to Cisco. Fortinet's Internet Service Database (ISDB) identifies thousands of applications for dynamic path steering, where Cisco relies on static IP whitelisting for many SaaS applications. Engineers migrating from Cisco to Fortinet consistently cite this as the most tangible operational improvement.
SASE coverage is the widest of the four vendors here. Fortinet has been recognized across SD-WAN, SSE, and ZTNA simultaneously, as the only vendor in this comparison to do so
Pricing is the most competitive on this list. Fortinet consistently prices below both Cisco and Palo Alto.
Where Fortinet Falls Short
FortiSASE is not cloud-native. FortiSASE runs FortiOS virtual machines in cloud PoPs rather than a purpose-built microservices architecture. At very large scale, typically 50,000 or more remote users, this VM-based approach has scaling limitations that cloud-native SSE competitors like Zscaler do not.
Support quality is mixed. Feedback from customers highlighted: "Most of the time, they send you just links and documents to read for troubleshooting. When you contact support, you don't need documents. You want someone that can understand your problem." Resolution speed at lower tiers is fast. Depth on complex issues is inconsistent.
Add-on licensing costs surprise buyers. Cloud sandboxing and advanced monitoring require separate subscriptions beyond the base SD-WAN license.
Firmware stability after updates is a documented concern. Customer reported instability following firmware upgrades. This is not a universal experience, but it surfaces often enough that production upgrade windows require careful change control planning.
Who It's Built For
Fortinet suits security-first organizations that want maximum branch-level threat protection without deploying separate security appliances at each site. It is particularly strong in regulated industries, financial services, healthcare, and government, and for organizations already running FortiGate firewalls who want to consolidate onto a single platform.
Palo Alto Networks Prisma SD-WAN
Architecture
Prisma SD-WAN, formerly CloudGenix and acquired by Palo Alto in 2020, is built on a cloud-native, application-centric architecture. Branch sites run ION appliances, hardware or virtual, that handle SD-WAN connectivity and application-based path steering.
Full NGFW security is intentionally absent from ION devices and is instead delivered through Prisma Access in the cloud as part of the Prisma SASE platform.
This is a deliberate architectural decision. Palo Alto's position is that branch security belongs in the cloud SASE fabric. ION appliances are optimized for path selection and application visibility.
Organizations requiring deep packet inspection at the branch must integrate Prisma SD-WAN with Prisma Access. The integration is well-built, but it is two systems, not one.
Precision AI drives automated path selection, application SLA enforcement, anomaly detection, and root cause analysis natively.

Where Palo Alto Is Strong
The SASE platform is the most architecturally complete on this list. Prisma SD-WAN integrates directly with Prisma Access (SSE), Prisma ZTNA, and Panorama for unified security policy. No other vendor in this comparison has a more coherent, cloud-native SASE story.
Application performance analytics are the strongest here. Prisma SD-WAN surfaces internet health data including latency, packet loss, and MOS scores per SaaS application in real time.
Zero-touch provisioning at scale is well-executed. Large branch rollouts are consistently rated as a deployment strength, and the cloud-managed provisioning model simplifies lifecycle management for distributed organizations.
Where Palo Alto Falls Short
ION appliances are not firewalls. This is the most important verification to make before entering a Prisma SD-WAN proof of concept. Deep branch security requires Prisma Access delivered from the cloud. For sites with strict local inspection requirements, compliance mandates requiring in-line security, or limited cloud connectivity reliability, this architectural model is a genuine mismatch.
Pricing is the highest on this list. Licensing is modular and many capabilities sit behind add-ons, which complicates procurement planning and total cost forecasting.
Support quality has declined. Feedback from customers highlighted: "Customer support is our biggest pain point. The quality of support has gone down since we initially deployed this product."
There is no CLI on ION devices. Engineers accustomed to command-line operations will find this a significant adjustment. Any new person attempting to access Prisma will have difficulty. It doesn't have CLI available."
The architecture favors hub-and-cloud topologies. Full-mesh or complex east-west branch-to-branch fabrics are harder to design and operate in Prisma SD-WAN. Organizations with significant branch-to-branch traffic should test this specifically during evaluation.
Who It's Built For
Prisma SD-WAN fits cloud-first enterprises that want the most complete SASE platform available and are prepared to deliver branch security through the cloud. It is strongest for organizations already invested in the Palo Alto security stack, and for large-scale deployments where consistent cloud-delivered policy enforcement across thousands of branches is the primary driver.
Also read: Zscaler vs. Netskope vs. Palo Alto vs. Cato: The SASE Selection Guide (2026)
HPE Aruba EdgeConnect SD-WAN
Architecture
EdgeConnect, formerly Silver Peak and acquired by Aruba/HPE, is a purpose-built SD-WAN platform with a clean separation between control, data, and management planes. EdgeConnect appliances sit at the WAN edge, physical or virtual, and Aruba Orchestrator handles centralized policy, provisioning, and monitoring.
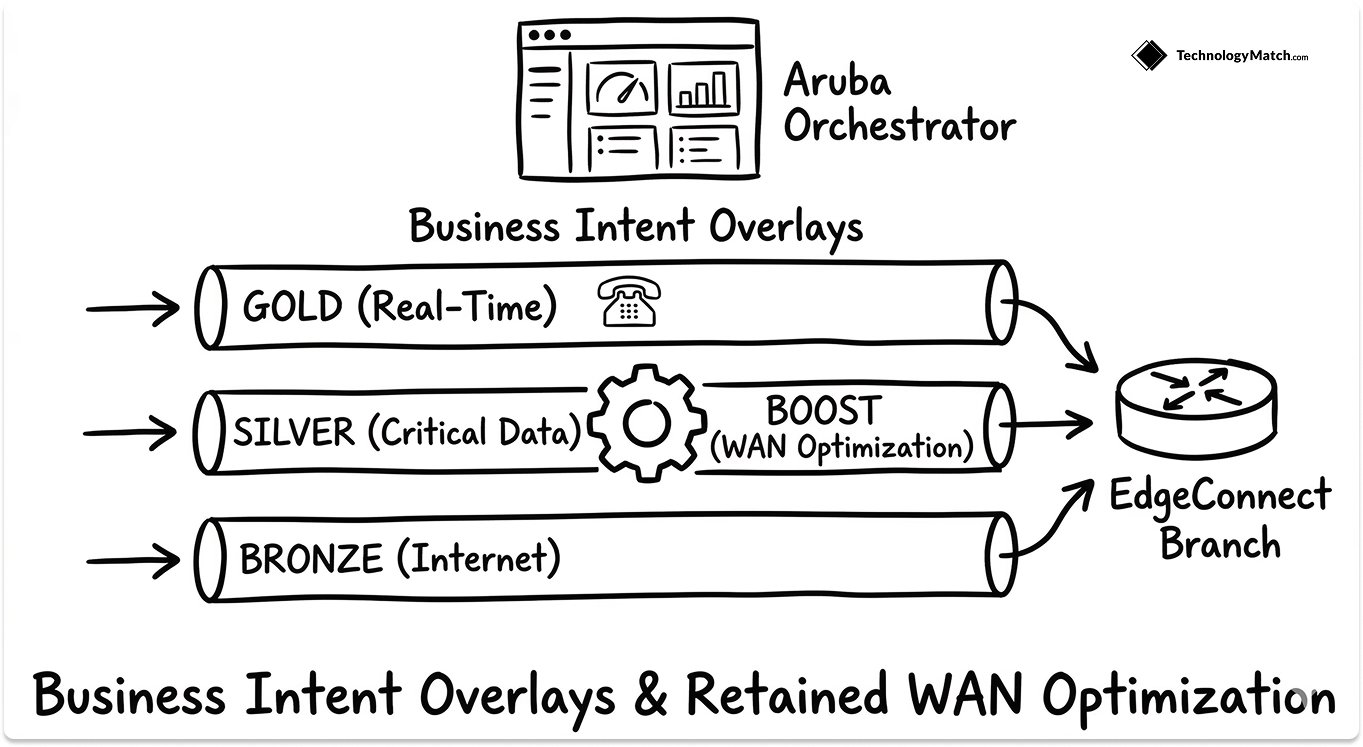
The platform is organized around Business Intent Overlays (BIOs), a policy model that maps application traffic to transport paths based on application type, security requirement, and business priority. This abstraction makes policy management accessible to teams without deep routing expertise.
EdgeConnect includes a built-in NGFW with IDS/IPS and role-based segmentation, enabling branch firewall consolidation without a separate appliance. The Boost add-on delivers TCP acceleration, data compression, and deduplication, WAN optimization capabilities most SD-WAN platforms have deprecated. EdgeConnect retained them.
Where HPE Aruba Is Strong
WAN optimization is a genuine, retained differentiator. Boost delivers TCP acceleration and deduplication for latency-sensitive applications, real-time voice, video, and legacy ERP. Where most SD-WAN vendors have stripped WAN optimization in favor of SASE positioning, EdgeConnect kept it. For organizations running applications sensitive to packet loss or high latency, this matters in practice.
Deployment simplicity and zero-touch provisioning are the best on this list. The model is: ship hardware to a branch, plug it in, it auto-registers and downloads configuration. In April 2025, a US hospital group deployed EdgeConnect across 140 outpatient sites using this model, cutting critical system outages by 50% and accelerating patient onboarding.
The management interface is the most accessible of the four vendors here. For IT teams without dedicated WAN engineers, the policy abstraction model in Orchestrator reduces operational overhead meaningfully compared to Cisco or Palo Alto.
Where HPE Aruba Falls Short
Security depth is the most significant gap on this platform. The built-in NGFW handles IDS/IPS and segmentation, but does not deliver UTM-level protection.
SASE integration is still maturing. HPE acquired Axis Security for SSE to complete its SASE story, but this integration is less native than Fortinet's single-OS approach or Palo Alto's purpose-built Prisma platform. A fully seamless single-vendor SASE experience from Aruba is still in development.
Licensing costs escalate sharply at renewal. Initial procurement pricing and renewal pricing diverge in ways that surprise buyers who did not negotiate renewal caps upfront.
Mindshare is contracting. EdgeConnect's mindshare in the WAN optimization category has dropped from 18.6% to 13.5% year-over-year, a trend consistent with the broader market shift toward SASE-first platforms.
Who It's Built For
HPE Aruba EdgeConnect suits mid-market to large enterprises that prioritize WAN performance, fast deployment at scale, and operational simplicity over deep security convergence. It is particularly strong in healthcare, retail, and distributed operations. Organizations with advanced security requirements should plan their SSE integration strategy carefully before committing.
SD-WAN Vendor Selector
Use the tool below to get a vendor recommendation matched to your environment.
Which Vendor Fits Your Organization?
If your WAN edge is your primary security surface, and you want branch-level threat protection without deploying separate security appliances at each site, Fortinet is the practical choice. The integrated ASIC-accelerated NGFW and single FortiOS eliminate the management overhead of parallel security stacks.
If you are already deep in the Cisco ecosystem with a large network engineering team and complex multi-carrier routing requirements, Cisco Catalyst SD-WAN is the path of least resistance. The routing depth and ecosystem integration are unmatched. Budget for complexity in licensing, deployment, and ongoing management.
If SASE is your 12-to-24-month roadmap and you want the most architecturally complete, cloud-delivered security story available, Palo Alto Prisma SD-WAN gives you the strongest platform. Plan to deliver branch security through Prisma Access in the cloud, and factor in a premium price.
If you have distributed operations, a lean WAN team, and need to move fast, HPE Aruba EdgeConnect delivers the best deployment experience and the most accessible management model. Go in clear-eyed about the security depth gap, and plan your SSE integration before you need it.
Questions to Ask Every Vendor Before You Sign
1. How is SD-WAN management separated from SSE management in your platform? Ask for a live demo with both visible simultaneously. Two management consoles mean two change control workflows, two support escalation paths, and two sets of policies to keep synchronized.
2. What is your SASE architecture at 500, 5,000, and 50,000 concurrent users? Ask whether SSE scales on cloud-native microservices or on VM instances. The architecture answer changes at scale, and the vendor's response will tell you how clearly they understand their own ceiling.
3. How is licensing calculated when we add 50 branches in year two, and what does renewal look like in year three? Get both answers in writing before signing. Renewal pricing in this market diverges significantly from initial procurement in ways that surprise most buyers.
4. What is your CVE track record over the last 24 months, and what is your average time from discovery to customer patch notification? Every vendor on this list has had vulnerabilities. The February 2026 CISA emergency directive on Cisco is a useful reference point for what poor disclosure timing looks like in practice. Ask what theirs looks like.
5. Can we speak to three reference customers at our scale, in our industry, in year two or later of deployment? Year-one references are easy to source. Year-two references reveal support quality, upgrade friction, and whether the sales-cycle promises held.
6. What does your AI and automation capability actually automate today without human intervention? Ask them to demonstrate a specific incident that was detected and resolved autonomously during a live proof of concept. If they cannot show it live, treat the capability as aspirational.
7. What is the migration path if we move to a different vendor in three years? A vendor confident in their product answers this without hesitation. Reluctance to answer it is itself a data point.
The SD-WAN decision in 2026 is an architecture decision that determines your SASE readiness, your security posture at every branch, and your operational overhead for the next five years. All four vendors here are credible options. None of them is the right choice for every organization. Run a structured proof of concept against the questions above, and the right answer for your environment will become clear.
Looking for SD-WAN vendors?
Get the shortlist right first. Tell us your environment, team size, and SASE requirements and we'll match you with vendors that fit. We can also prep the vendors so your conversation begins with context. And it's free.
FAQ
Which SD-WAN vendor is best for enterprise use in 2026?
No single vendor wins for all enterprises. Fortinet leads on security integration, Cisco on routing depth, Palo Alto on SASE completeness, and HPE Aruba on deployment simplicity. The right choice depends on your infrastructure, team, and security model.
What is the difference between Fortinet SD-WAN and Cisco SD-WAN?
Fortinet runs its NGFW and SD-WAN on the same device under one OS — no separate security appliance needed at each branch. Cisco has deeper routing capabilities and a broader enterprise ecosystem, but its security stack requires separate products and its SASE management runs across two consoles.
Does Palo Alto Prisma SD-WAN include a firewall?
No. ION appliances handle connectivity and path selection only. Security inspection requires Prisma Access delivered from the cloud. Organizations that need local firewall inspection at each branch should verify this fits their compliance requirements before evaluating Prisma SD-WAN.
What is the most affordable SD-WAN solution for mid-market companies?
Fortinet and HPE Aruba EdgeConnect are the most cost-competitive options. Fortinet offers better security-to-cost ratio and more predictable licensing. Aruba is faster to deploy but its renewal pricing escalates more sharply — factor that into your five-year TCO.
Which SD-WAN vendors support SASE in 2026?
Palo Alto has the most complete single-vendor SASE architecture. Fortinet covers SD-WAN, SSE, and ZTNA under one vendor but uses a VM-based cloud architecture. Aruba's SASE integration is still maturing. Cisco was excluded from the Forrester SASE Wave in Q3 2025 for lacking a unified management plane.